Sensitive information, such as bank details, private conversations, and intimate photographs, is exposed or leaked daily. In fact, it is reported that ransomware attacks happen every two seconds. With new data breaches and hacks emerging around the world, individuals, companies, and governments have become more vigilant about cybersecurity. Striking a balance between awareness and paranoia is crucial when it comes to online activities.
How Does Hacking Work?
Hackinginvolves gaining unauthorized access to computer systems or networks with the intent to exploit vulnerabilities or gather sensitive information. This typically includes activities such as probing for weaknesses, exploiting security flaws, and often employing various techniques to bypass or compromise security measures. The specific methods and tools hackers use can vary widely, but the ultimate goal is to manipulate or gain control over a system, steal data, disrupt services, or achieve other malicious objectives.
How Do Hackers Get into Your Computer?
Hackers can gain access to your computer through various methods, including: Malware: They may trick you into downloading malicious software (e.g., viruses, Trojans, spyware) via email attachments, fake websites, or compromised downloads.
Interesting: Signs of Malware: How to Know if Your Computer is Infected
Phishing: Hackers use deceptive emails or messages to trick you into revealing sensitive information like login credentials or installing malicious software. Weak passwords: If you have weak or easily guessable passwords, hackers can use brute force attacks or password-cracking tools to gain access. Vulnerabilities: Exploiting software or system vulnerabilities is another method. Outdated or unpatched software can be susceptible to such attacks.
Expert tip: [EASY GUIDE] How to Update Device Drivers on a Windows 10 PC?
Remote access: Hackers can exploit remote desktop or file-sharing services if they are not securely configured.
Related: How Secure is Cloud Storage: Security Issues and Solutions
Social engineering: Manipulating individuals through social engineering tactics to divulge information or grant access. Physical access: In some cases, hackers may physically access your computer to install malware or tamper with hardware.
Can a Computer Be Hacked if It Is Turned Off?
In most cases, a computer that is completely turned off (not in Sleep or Hibernation Mode) is less vulnerable to remote hacking. When a computer is powered off, its operating system and software are not actively running, which means there are fewer attack surfaces for hackers to exploit. However, there are a few scenarios where a computer could still be vulnerable even when turned off:
- Physical access: If an attacker has physical access to the computer, they may be able to compromise it, for example, by installing malicious hardware or tampering with the system.
- Wake-on-LAN (WoL): Some computers have Wake-on-LAN functionality enabled by default. This allows them to be powered on remotely using network signals. If an attacker has access to the local network and knows the computer’s MAC address, they might be able to turn it on and attempt an attack.
For instance with “wake on LAN,” the computer can be configured to respond to remote instructions. A special signal can be sent to the computer over a shared network, allowing the hacker to power it back on and access any data they’d need. Without appropriate security software installed, such as anti-malware tools like Auslogics Anti-Malware, it is possible for hackers to access the computer remotely even if it is turned off. Such a scenario is likely in corporate settings where there are circumstances that require individuals to set computers to “wake on LAN.”
- Firmware exploits: In rare cases, sophisticated attackers may exploit vulnerabilities in a computer’s firmware or hardware, allowing them to compromise the system even when it’s powered off.
What to Do if Your Computer Is Hacked
Things to Do Immediately
Quarantine your PC during a security breachWhen dealing with a compromised computer, immediate isolation is essential. While your computer remains connected to the internet, hackers maintain access to your device and its files. You don’t necessarily need to sever the network cable; however, you should disconnect your computer from the network and avoid all forms of wireless and physical connections. The objective is to halt the virus from spreading any further. Ensure that you are completely offline, deactivating all Wi-Fi connections through both software settings and hardware controls. Some laptops are equipped with a physical switch for this purpose. Why is it crucial to disconnect hardware? Hacking software can be remarkably sophisticated, sometimes deceiving your computer into appearing disconnected while the malware quietly wreaks havoc in the background. Change your passwordsIn 2023, the task of guessing straightforward passwords, especially those lacking significant length or complexity, has become rather effortless for hackers. To put it into perspective, if your password contains fewer than 10 characters, it could be deciphered within a mere two weeks. Even a relatively uncomplicated 10-character password comprised solely of numbers or lowercase letters may succumb to hacking in less than 24 hours. Begin by changing the access password on your PC. Subsequently, overhaul all your passwords from an unaffected computer or smartphone, including your email, social network accounts, subscriptions, and any other services you use. Each of these accounts houses valuable information, including personal data and financial details.
Remember, a single compromised password could potentially grant access to a multitude of accounts.
According to the Cybersecurity & Infrastructure Security Agency (CISA), certain criteria should be adhered to when crafting secure passwords:
- Opt for a password length ranging from 8 to 64 characters; the longer, the better.
- Don’t use personal information, such as your name, birth date, or company name. Flex your creativity and make it unique.
- Make sure your new password is different from your previous passwords and those used for other accounts.
- Construct your password by drawing characters from all four categories: lowercase, uppercase, numbers, and symbols.
- Using a password manager simplifies the process of updating passwords and grants additional security benefits such as Two-Factor Authentication (2FA) and the generation of temporary passwords.
Related:Stay Safe Online: The Best Ways to Store Passwords
Secure your data: Power down and remove the hard driveWhen your computer falls victim to compromise, swift action is imperative to safeguard your data. Here’s a recommended course of action:
- Immediately power down your compromised computer to prevent any further damage to your files.
- After shutting down, carefully remove the hard drive from the affected computer. This hard drive can then be connected to another computer as a secondary, non-bootable drive.
- The secondary computer you connect the hard drive to should be equipped with up-to-date anti-virus and anti-spyware software to scan the extracted drive thoroughly.
- If you decide to connect the drive internally instead of using a USB caddy, ensure that the dip switches on the back of your hard drive are configured as a secondary drive. Setting it as the primary drive may trigger attempts to boot the secondary PC using your operating system, potentially causing further complications.
- If you’re not comfortable with the process of removing the hard drive yourself or lack access to a spare computer, it’s advisable to seek the assistance of a reputable local PC repair shop.
Inspect your drive for infections and malwareUse the anti-virus, anti-spyware, and anti-rootkit scanning tools on the alternate host PC to thoroughly detect and eliminate any infections present within your hard drive’s file system. Here’s an example of how to scan your drive using Auslogics Anti-Malware:
- Download and install Auslogics Anti-Malware from the official website.

- Launch the program.
- Choose the type of scan you want to perform: quick scan, custom scan, or deep scan (recommended).
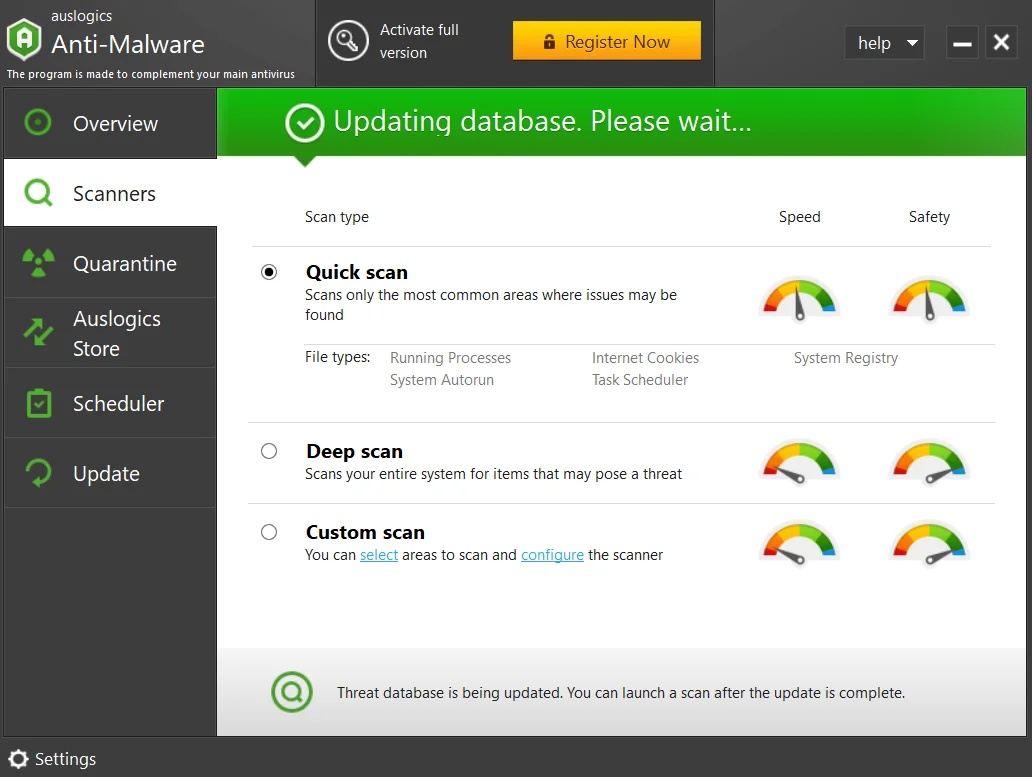
- Once the scan is complete, you will get a detailed report of all the issues detected.
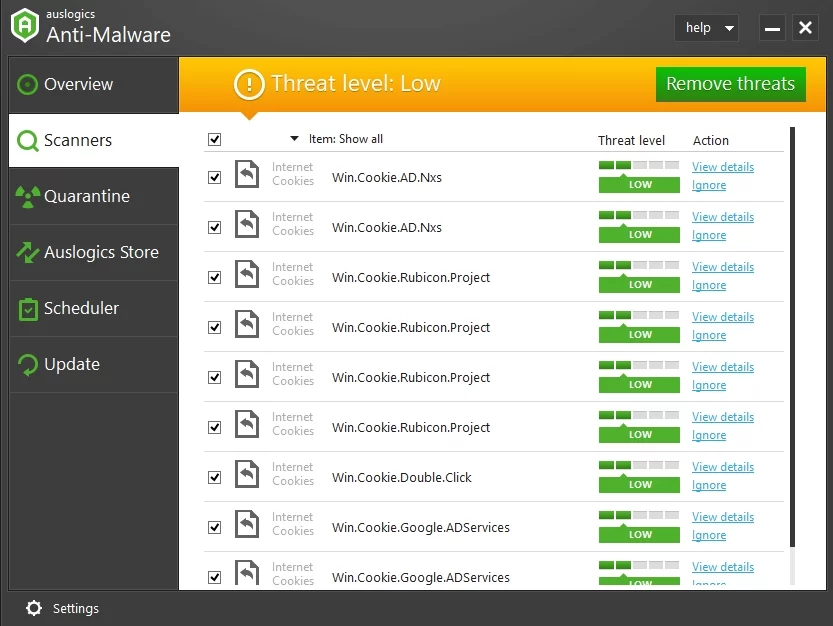
- Follow the on-screen prompts to proceed.
Related:Auslogics Anti-Malware: Features and Reviews
Wipe your hard drive (if necessary)In the event of a virus or hack discovery, it may become necessary to completely wipe your hard drive and perform a fresh operating system installation. This process, known as wiping, involves the complete removal of data, so it’s crucial to note that anything deleted will be irretrievable unless you create backups beforehand. Note that deleted files can still linger on your hard disk. Opt for downloadable software designed for secure data wiping. A proper wipe, much like a virus scan, will provide a clear notification once the process has been successfully completed.
Also Read: Windows 10 Backup Guide: Backing Up to an External Hard Drive
Safeguard your crucial data from the previously compromised drivePrioritize the retrieval of all your essential data from the previously compromised drive. Copy your photos, documents, multimedia content, and any other personal files onto a secure medium, such as DVDs, CDs, or an untainted hard drive.
Also Read: How to Find Duplicate Files – Introducing Auslogics Duplicate File Finder
When You Are Ready
Reinstall the operating system using verified media and apply updatesRetrieve your original OS disks, either the ones you purchased or that were supplied with your computer. Avoid using copies from unverified sources, as relying on trusted media is essential to prevent potential reinfection by viruses lurking on tainted operating system disks. Before proceeding further, ensure that you download and apply all available updates and patches for your operating system. This step is crucial for enhancing security.
Also read:How to Get And Use Windows 10 Media Creation Tool
Reinstall security software, including anti-virus and anti-spyware toolsPrioritize the installation and updating of all your security-related software. It’s vital to ensure that your anti-virus software is fully up-to-date before introducing any additional applications. This precaution helps uncover any malware that might be concealed within other applications, especially if your virus signatures are not current.
Also read: How to Keep Your Software Up to Date
Scan your data backup disks for potential virusesEven if you have confidence in the cleanliness of your data files, it’s prudent to conduct virus scans on your data backup disks before reintegrating them into your system. This added layer of scrutiny ensures that no lurking threats are inadvertently introduced. Create a comprehensive system backupOnce your system is in pristine condition, it’s wise to generate a comprehensive backup . This precautionary measure can significantly expedite future recovery processes in case of similar incidents. Consider utilizing a backup tool that produces a bootable hard drive image as part of your backup strategy to streamline and accelerate future recoveries. Inform your network to prevent further spreadHackers often spread through one person to target their network. They use your email to send messages that seem trustworthy. So, before unintentionally spreading a virus, protect your close contacts and inform them to stop the attack.
Also Read: Digital Privacy: Tips on How to Protect Yourself on the Internet
How to Prevent Hacker Attacks When Your PC is Turned Off
While a turned-off computer is less susceptible to hacking, there are still additional security measures you can put in place to make remote hacking impossible:
1. Implement Full-Disk Encryption:
- Choose a reputable full-disk encryption software. Popular options include BitLocker (for Windows), FileVault (for macOS), and VeraCrypt (cross-platform).
- Install and configure the encryption software on your computer.
- During setup, you’ll typically create a strong encryption password or passphrase. Ensure it’s complex and unique.
- Follow the software’s instructions to encrypt your entire hard drive. This process may take some time, so be patient.
- Once encryption is complete, your data is secure. Whenever you start your computer, you’ll be prompted to enter your encryption password or passphrase to access the data.
2. Set a BIOS/UEFI Password:
- Restart or turn on your computer and access the BIOS/UEFI settings. This is usually done by pressing a specific key during boot, like F2, F10, or Delete. Check your computer’s manual for the correct key or look for on-screen prompts during startup.
- In the BIOS/UEFI settings, navigate to the security or password section.
- Look for an option to set a BIOS/UEFI password. Depending on your computer’s manufacturer and model, this option may be labeled differently.
- Create a strong BIOS/UEFI password. Ensure it’s unique and not easily guessable.
- Save your changes and exit the BIOS/UEFI settings. Your computer will now prompt you to enter the BIOS/UEFI password whenever you boot it or attempt to access the BIOS/UEFI settings.
3. Enable Security Features Like Secure Boot:
Secure Boot is a security feature designed to enhance the integrity of a computer’s boot process. When enabled, it ensures that only trusted and digitally signed software, such as the operating system and bootloader, can run during startup. This helps prevent the execution of malicious or unauthorized code that could compromise the system’s security. Enabling Secure Boot is a good idea on a PC because it provides a strong defense against various types of malware and unauthorized system modifications, enhancing the overall security posture of the computer and safeguarding sensitive data and processes.
4. Install Trusted Anti-Malware Software:
The first line of defense against cyber threats is reliable anti-malware software. Once an intruder breaches your computer’s defenses, safeguarding your sensitive information can become a race against time. Rather than attempting manual malware removal, opt for a robust anti-malware tool like Auslogics Anti-Malware. It can automatically detect and neutralize threats, providing you with real-time protection.
5. Implement Two-Factor Authentication (2FA):
Leverage the added security of two-factor authentication (2FA) when available, especially for critical accounts like Gmail or LinkedIn. With 2FA, even if a hacker somehow obtains your password, they still face an additional barrier before accessing your information. Typically, you’ll receive a secret code via SMS when someone attempts to log into your account.
Conclusion
While a completely turned-off computer is less vulnerable to remote hacking, it’s essential to remain vigilant about physical security, regularly update your software, and adopt best practices for online and offline protection. While the risk is reduced when your computer is off, taking proactive measures is key to maintaining a secure digital environment. The fight against hacking is an ongoing battle, and every bit of knowledge helps. Do you have alternative strategies or suggestions to protect against hacking attempts? We welcome your insights and ideas in the comments below. Together, we can fortify our digital defenses and create a safer online environment.
FAQ
- Implement full-disk encryption to protect the contents of your hard drive.
- Set a BIOS/UEFI password to prevent unauthorized access to your computer’s settings.
- Enable security features like Secure Boot to defend against malicious software.
- Use strong, unique passwords for your accounts.
- Implement full-disk encryption to secure the entire hard drive.
- Set a BIOS/UEFI password to restrict access to your computer’s settings.
- Enable security features like Secure Boot to prevent unauthorized software execution.
- Regularly back up your data to an external, secure storage device or cloud service.
- Be cautious of physical security threats and safeguard your computer against theft or tampering.
