What is Phishing?
Phishing is an internet scam where malicious individuals pretend to be from a reputable and well-known company. The goal is to lure you into disclosing sensitive information like passwords, credit card numbers, or personal information.
In other words, these scammers use social engineering schemes to lure you with trust to try and get crucial information from you. This can be your social media login or social security number.
The scammers attempt to persuade you to open malicious emails , complete a form, click a link, or share private information.
Types of Phishing Attacks
Scammers use different phishing techniques to attack their victims. They often use the same method but change the tactic depending on who they’re trying to trick and how they go about it.
Here are the types of phishing attacks:
Spear Phishing
Consider using a pole to go fishing. You might catch a variety of aquatic life. However, when you use a shart spear, you can only target a specific fish. And that’s where the name comes from. Spear phishing focuses on deceiving a particular group or individual, such as a person in charge of a company’s computer network.
Whaling
Whaling is a mainly targeted form of phishing that targets huge targets. It’s similar to aiming for whales in the ocean rather than common fish. These attacks frequently target prominent individuals within a company, such as the CEO and CFO. For example, your company may be difficult, and a whaling email may advise you to click a link for further information. After clicking a phishing link , you’ll be redirected to a page asking you to reveal crucial business information like tax ID and bank account details.
Email Phishing
Email phishing is the most common way for scammers to trick you. These fraudulent people send numerous emails telling you your account is in trouble and you must immediately click a link. There are different types of phishing emails . However, they usually contain writing errors, making these tactics easy to spot. However, you’ll find some with excellent grammar and spelling. There are different signs of a phishing email. You can look at the source of the email and the link they want you to visit to verify whether they’re legitimate. If anything appears fishy, it might be a scam.
How to Spot Scams
Phishing scams usually pose as a reputable organization. How to tell if an email is a scam? Even though scammers are skilled at making these methods appear genuine, there are ways to recognize them.
Let’s find out:
Recognizing Phishing Emails
Scammers create stories to trick you into clicking links or downloading attachments in their emails. They may insist that you confirm personal information or that your account has a problem.
Even better, they might provide gifts or a refund. But here’s how to recognize the scam:
- The email claims your account is in trouble even though you’ve done nothing wrong.
- The scammers want you to click a link, but that link can include malicious malware.
- They request money or personal information, but legitimate businesses wouldn’t do that over email.
- You receive an invoice for something you didn’t purchase from them.
- They provide a freebie that seems too good to be true.
Keep reading – we will speak in more detail on how to identify phishing emails.
Identifying Suspicious Links
Scammers may include links that seem legitimate but are actually harmful in their emails. These links may install malicious software on your computer after you’ve clicked on a phishing link.
Here’s how to identify if a link is safe and take precautions:
Email phishing has been around for almost two decades, but many people still fall victim to it. This is no laughing matter as big corporations, tech giants and even digital security companies have experienced data breach through this scam.
So, how can you protect yourself from email phishing schemes? In this article, we will provide a comprehensive discussion on how this scam works so you can understand how to avoid phishing attacks. We’ll also provide email safety tips that will help you keep your online activities secure.
- Without clicking, move the mouse pointer over the link. It’s usually a scam if the web address appears unusual or changed.
- Verify that the link matches the company’s official website and that it begins with “https” (the “s” is key).
Paying Attention to Website Security
Sometimes scammers develop fake websites that look like legitimate ones. On these websites, they want you to enter your information. Here’s how to be safe:
- Take a close look at the website address. It’s probably a fake if it’s misspelled or appears strange.
- A padlock icon should appear next to the website address. This shows that the website is secure.
Related:Digital Privacy: Tips on How to Protect Yourself Online
How to Protect Yourself from Phishing
If you want to know how to prevent phishing, follow the below methods:
1. Use Strong and Unique Passwords
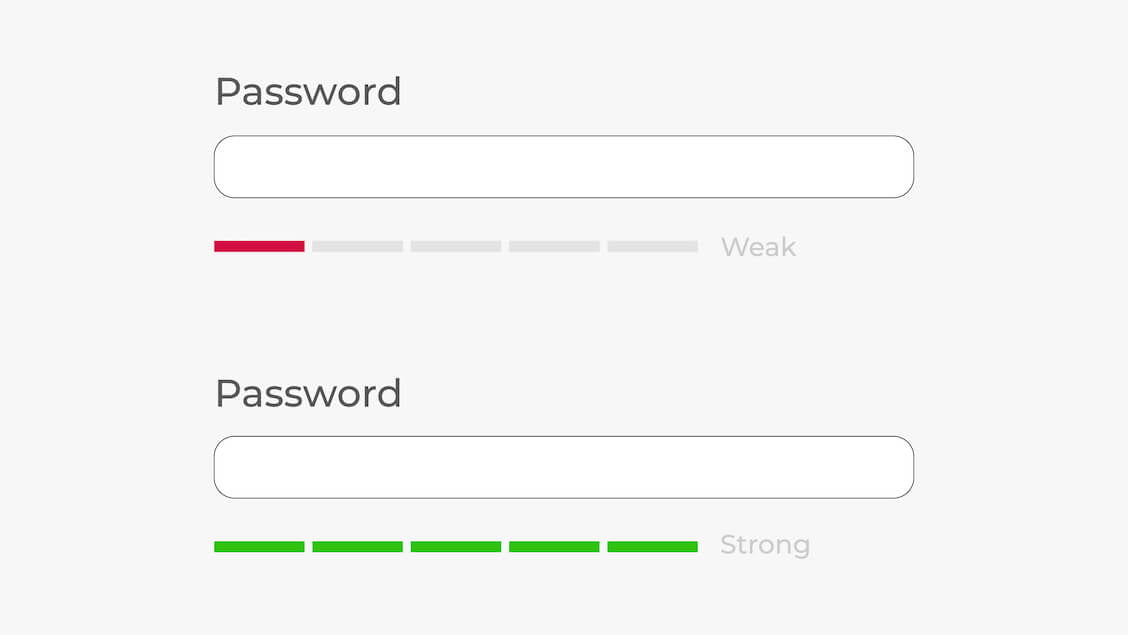
Your first line of security should be to create solid and one-of-a-kind passwords. A mix of capital and lowercase letters, digits, and special characters makes up a strong password. You should avoid information like birthdays or frequent nouns.
Also, make sure that each online account has a unique password to prevent a compromise from affecting many accounts.
Related:Stay Safe Online: The Best Ways to Store Passwords
2. Enable Two-Factor Authentication (2FA)

Your accounts have an additional degree of security thanks to two-factor authentication. Even if a scammer can get their hands on your password, they won’t be able to access your account without the additional verification step if the 2FA is activated.
You can use an authentication app, email, or text message to receive a verification code.
Related: How to Turn Off Two-Factor Authentication?
3. Keep Software Up to Date
It’s crucial to regularly update your operating system, software, and antivirus programs. These updates frequently come with patches for security flaws that scammers could use.
Set your devices to automatically update so you always have the most up-to-date defense against new threats.
Related: How to Keep Your Software Up to Date
4. Utilize a Reputable Antivirus Program
Install a reliable antivirus program to find and remove harmful software from your devices. Antivirus software can help you stop phishing attacks by spotting questionable links, attachments, and websites.
Keep your antivirus program updated to keep safe from any emerging threats.
Also Read:How to Remove Virus and Other Malware from Windows
How to Identify Phishing Emails
There are certain precautions you need to take to prevent phishing attacks. So if you want to know how to prevent phishing, check the below strategies:
1. Check the Sender’s Email Address
If you want to know how to identify phishing emails, the first thing is to check the sender’s email address. Email addresses used by scammers frequently resemble real ones on the surface but differ slightly.
When receiving official emails from well-known organizations, be careful of email addresses that use popular free email domains like “@gmail.com.” Usually, legitimate organizations use their domain names, such as “@company.com.”
2. Look for Spelling and Grammar Mistakes
Spelling, grammar, and punctuation mistakes are all signs of a phishing email. Scammers might not pay as much attention to detail as trustworthy businesses. Check the email carefully for any strange wording or grammatical errors pointing to fake communication.
Genuine messages from reliable sources typically keep a high standard of writing professionalism.
3. Analyze Email Content for Urgency
Phishing emails usually evoke a sense of urgency or panic to get you to act quickly. Be careful of notifications warning you that your account will be suspended, that it has been compromised, or that you need to take quick action to avoid penalties.
Scammers try to intimidate you into making quick decisions without giving you much thought. So independently confirm the information through official means before making any decisions.
What to Do If You Click on a Phishing Link
If you’ve clicked on a phishing link, don’t worry. There are steps you can take immediately to lessen the possible damage. If you ever find yourself in this situation, follow the below steps:
1. Disconnect from the Internet
Disable Wi-Fi or unplug the network wire to cut off your connection to the internet immediately. This helps stop your device from communicating with the malicious website or service in the future.
By disconnecting, you can reduce the likelihood of a data breach or the theft of sensitive information.
Also Read: How to Check Wi-Fi Password on Windows 10/11 Computer in Seconds
2. Scan Your Device for Malware
Make careful to follow the software's removal guidelines for any risks it detects.
3. Change Your Passwords
You should immediately change the passwords of the accounts you visited after clicking the phishing link. Your email, social media, banking, and other online accounts can be this. Use strong, one-of-a-kind passwords to increase the security of your account.
You can also enable two-factor authentication as an additional measure of security.
4. Report the Phishing Attempt
Inform the appropriate authorities or organizations about phishing attacks. Numerous websites and email service providers have directions for reporting phishing scams.
By alerting authorities, you support efforts to stop additional fraud and keep others from becoming victims.
Conclusion
Phishing attacks can be frustrating and dangerous if you don’t immediately stop them, especially if you’ve clicked on a phishing link. Luckily, you can know how to prevent phishing attacks by following the steps in this guide.
After taking these quick precautions, be on the lookout for any strange activity or unauthorized access to your accounts, and remain cautious.
Keep a regular eye out for fraudulent activities or changes in your online accounts and financial statements.
Remember that taking prompt, decisive action can help protect your digital identity and sensitive information by significantly reducing the potential effect of a phishing incident.
FAQ
You can assist other people in avoiding becoming victims by reporting the phishing email to your email provider and the appropriate authorities.
