- What Is BitLocker Drive Encryption?
- Is Windows Device Encryption different from BitLocker?
- How Does BitLocker Work?
- Windows BitLocker System Requirements for Windows 10 and 11
- How to Enable Windows BitLocker on Windows 10 and 11
- How to Disable Windows BitLocker on Windows 10/11
- How BitLocker Encryption Compares to Other Windows Encryption Tools
- Common Concerns Users Have with BitLocker Encryption and How to Fix Them
- Best Practices of BitLocker Encryption for Online Safety
- Protect Your Data with BitLocker Drive Encryption: Final Thoughts
- FAQ
Protecting your data has become more crucial than ever, especially in the AI era we are in. Lucky for us, Microsoft has made it easier by automatically enabling BitLocker Drive Encryptio n on PCs (at least for most of the modern ones).
So you don’t have to go through complex security settings to secure your personal data. All you have to do is sign in to your Microsoft account. But what exactly is Windows BitLocke r? How does it work, and is it any good?
Do you really need it, or should you stick with third-party tools? I’ll answer these questions and walk you through simple ways to enable the feature.
What Is BitLocker Drive Encryption?
BitLocker is Microsoft’s storage encryption technology on Windows PCs designed to secure your data by encoding it. So, if you enable BitLocker on your primary drive (which is usually labeled C:), every piece of data on it will get encrypted.
You can also use the BitLocker encryption to encrypt other drives, like external hard drives. If someone gains unauthorized access to your computer, they won’t get access to your data without the encryption key or password.
Is Windows Device Encryption different from BitLocker?
Most people confuse Device Encryption with BitLocker, thinking they are the same. Well, they are not, even though they basically perform the same function. And they are all from Microsoft.
Later, I’ll compare various Windows encryption tools with BitLocker, including Device Encryption, to give you more clarity. But what you need to know now is that Device Encryption automatically encrypts your hard drive, and it’s done by default.
This makes it faster, but it’s not as customizable as BitLocker. Here’s a table comparison between the two:
| Feature | Windows Device Encryption | BitLocker |
|---|---|---|
| Availability | Windows Home and Pro (if hardware supports it) | Windows Pro, Enterprise, and Education only |
| Encryption coverage |
|
Locks specific or removable drives, entire disk, partitions |
| Customization | Can’t encrypt specific drives or partitions | Highly customizable |
| Speed | Generally faster than BitLocker | Slower because of its broader feature set |
| Hardware requirements | TPM (1.2 or 2.0), UEFI Secure Boot, DMA protection enabled | TPM (1.2 or later), TCG-compliant BIOS or UEFI |
| Use case | Basic data security for personal devices | Advanced encryption for enterprises and professional users |
How Does BitLocker Work?
Here’s how BitLocker on Windows 10 or 11 essentially works:
How the encryption works
BitLocker uses the Advanced Encryption Standard (AES), which is either in 128-bit or 256-bit keys. When you activate BitLocker, it encrypts each bit of data on your hard drive.
In other words, instead of encoding files one by one, it encrypts the entire volume to make sure your data is more secure.
After that, the encryption key is stored securely, using mostly the Trusted Platform Module (TPM) chip. By the way, this chip is a security hardware component in many modern PCs used for generating, storing, and managing cryptographic keys.
If your computer doesn’t have a TPM chip, you can change the settings to store the key on a USB drive or use a password or PIN.
An encryption key is basically a string of characters that transforms plain text into an unreadable format and vice versa. BitLcoker creates it by generating a Full Volume Encryption Key (FVEK) and a volume master key (VMK).
The FVEK locks the actual data while the VMK encrypts the FVEK. Then, both keys are stored in either the TPM, USB drive, or password, depending on the settings you use.
How decryption happens during startup
BitLocker decryption happens very early in the boot process when you turn on your computer. It begins when the BIOS hands over control to the OS loader. If you encrypted your primary drive, the decryption starts right after the PC starts.
BitLocker first checks to see if any tampering has occurred since the last shutdown by comparing the system’s stored values with the current boot sequence.
If everything checks out, BitLocker will unlock the VMK, and the VMK will then decrypt the FVEK.
From there on, the operating system decodes data on the fly as other apps and OS access it. In other words, the decryption happens in real time.
You might be thinking that if the decryption occurs in real time, then it consumes too many resources, and that can affect system performance. But that’s not the case. You see, the entire process is optimized to have minimal impact on your PC performance.
And most current CPUs are designed to handle these types of decryptions efficiently so that the process doesn’t cause noticeable delays.
Different BitLocker authentication options for unlocking your drive:
| TPM-only mode | This mode automatically unlocks the drive without you needing to enter any password or PIN or doing anything at all. |
| TPM + PIN | You have to enter your PIN to get access. It adds an extra layer of security. |
| TPM + USB key | You must insert a USB with the decryption key at startup to log in. |
| TPM + PIN + USB key | You must enter a PIN and insert a USB key to gain access. This offers the highest level of protection. |
How data stays protected
I’ve already mentioned how Windows 10 or 11 BitLocker decrypts data as you access files. Let’s go a bit more in detail. The unlocked data is stored in memory at the moment you need it.
That means when the system shuts down or loses power, the data on the hard drive is still encrypted and thus protected. When you add new data or information, BitLocker encrypts it before it’s saved on the drive.
Again, the entire process happens in real time and doesn’t affect how your system performs. So you should have no problem.
How to get back in if locked out
Sometimes, Windows BitLocker may fail to start, for example, due to hardware changes or corrupted TPM. When this happens, you’ll be prompted with a 48-digit recovery key, which you should have when setting up BitLocker on Windows 10 or 11.
📌 Related read: BitLocker Recovery Key: How to Avoid Losing It and What to Do if You Do
Windows BitLocker System Requirements for Windows 10 and 11
BitLocker has a few system requirements that are slightly different between Windows 10 and 11. Let’s quickly go through them:
- Operating system versions. BitLocker is available on Windows Pro, Enterprise, and Education editions on both Windows 10 and 11. Windows 10 or 11 Home doesn’t support BitLocker, so you’ll have to upgrade if you’re using this version.
- TPM version required. Ideally, BitLocker in Windows 10 needs a TPM version 1.2 or later, even though the 2.0 version is recommended. However, Microsoft has mandated TPM 2.0 for all Windows 11 installations. That means your Windows 11 PC should already have this version by default.
- Type of firmware needed. BitLocker is available on Windows 10 devices with either BIOS or UEFI firmware. However, it’s better to get UEFI with Secure Boot for extra security. But if you’re using Windows 11, having a UEFI firmware with Secure Boot is a must.
Here’s a table comparison:
| Feature | Windows 10 requirements | Windows 11 requirements |
|---|---|---|
| Operating system | Windows 10 Pro, Enterprise, or Education | Windows 11 Pro, Enterprise, or Education |
| TPM | Version 1.2 or higher (2.0 recommended) | Version 2.0 or higher |
| BIOS/UEFI compatibility | UEFI firmware with Secure Boot recommended | UEFI firmware with Secure Boot required |
| Storage drive type | Internal drives (HDD or SSD) | Internal drives (HDD or SSD) |
How to check if your PC supports the TPMFollow the simple steps below to ensure your computer can support Windows 10 or 11 BitLocke r:
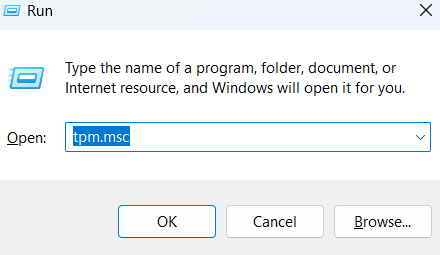
- Get the Run dialog box running by pressing Windows key + R.
- Then type “tpm.msc” and press Enter.
- The TPM Management window will open, showing you all the details of the TPM version, including its status on your PC. Otherwise, you’ll get the message “Compatible TPM cannot be found.”
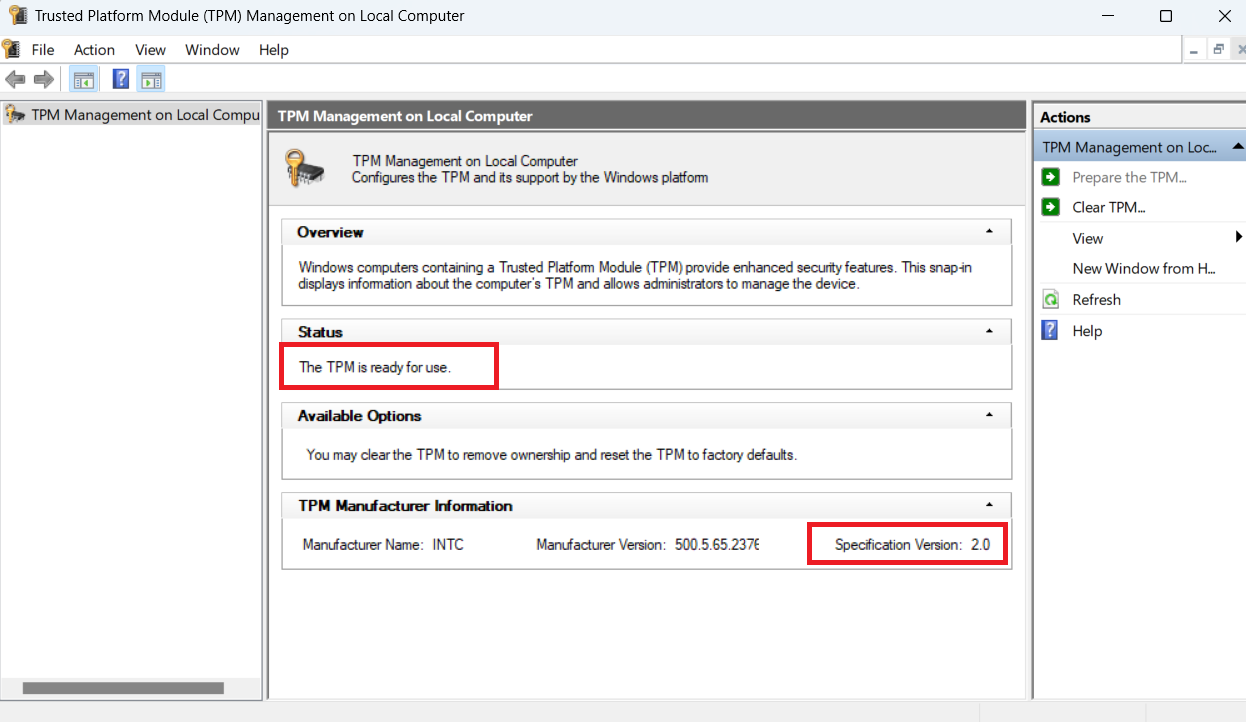
If your PC doesn’t have a compatible TPM, you can enable it via the BIOS/UEFI settings, updating the firmware, or reinstalling the TPM driver. In some cases, clearing the TPM keys can also fix the problem.
However, if the TPM isn’t supported, you’ll have to enable Windows BitLocker without the TPM or use third-party encryption software like VeraCrypt .
How to Enable Windows BitLocker on Windows 10 and 11
Enabling BitLocker on Windows 11 is the same as on Windows 10 with minor differences. Regardless, following the steps below shouldn’t be a big issue if you use Windows 10.
Also, I’ll be showing you how to enable BitLocker Drive Encryption on your system drive, removable drives, and devices without TPMs.
How to enable BitLocker on hard drive
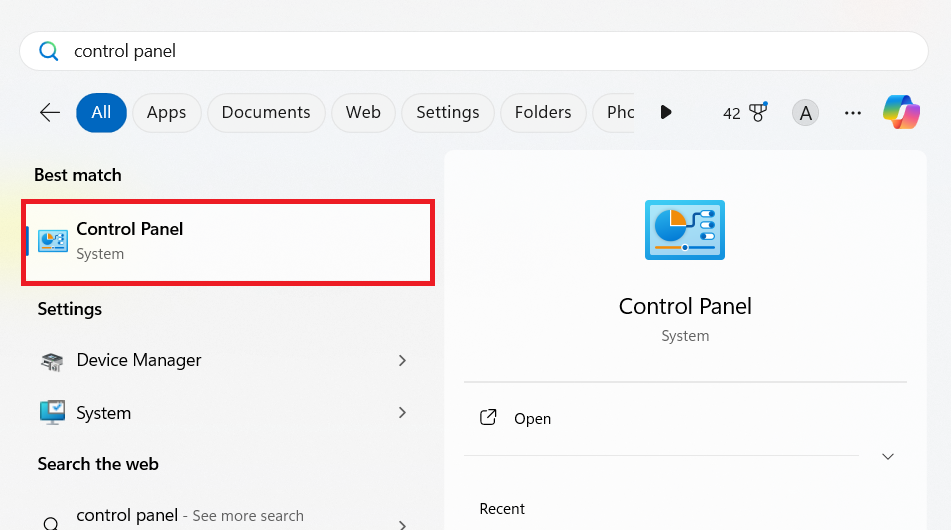
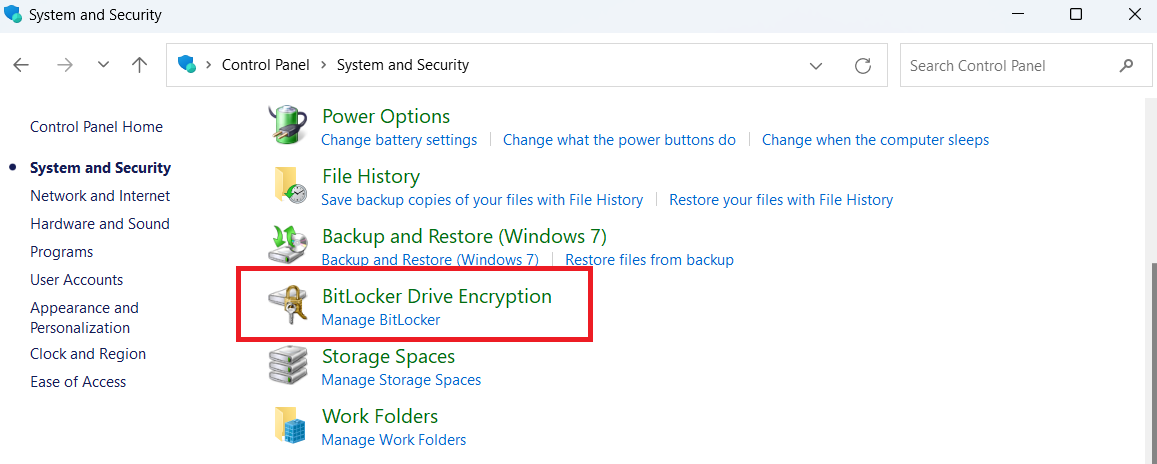
- Open the Control Panel by typing “control panel” in the search box and clicking on it
- Go to System and Security. Make sure View by is set to Category .
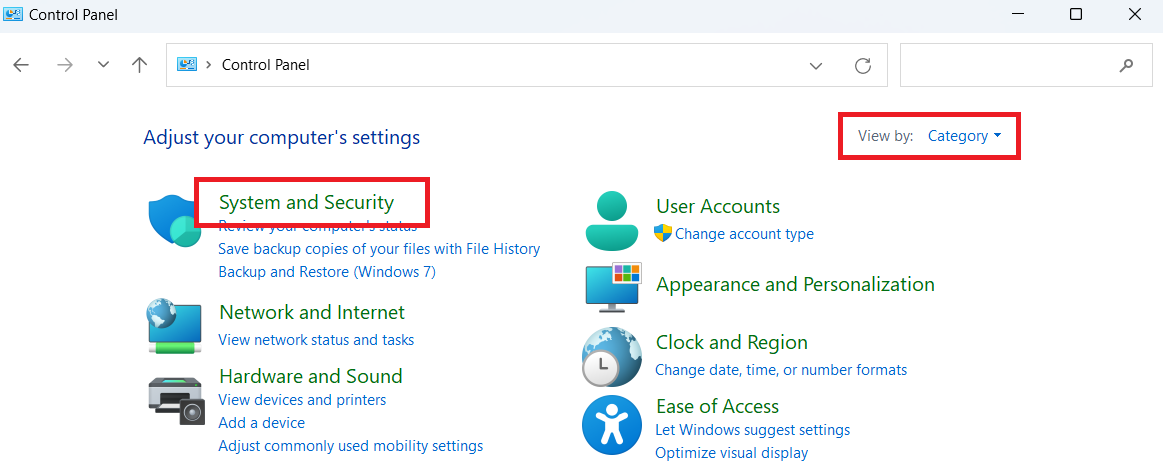
- Scroll down and click on BitLocker Drive Encryption .
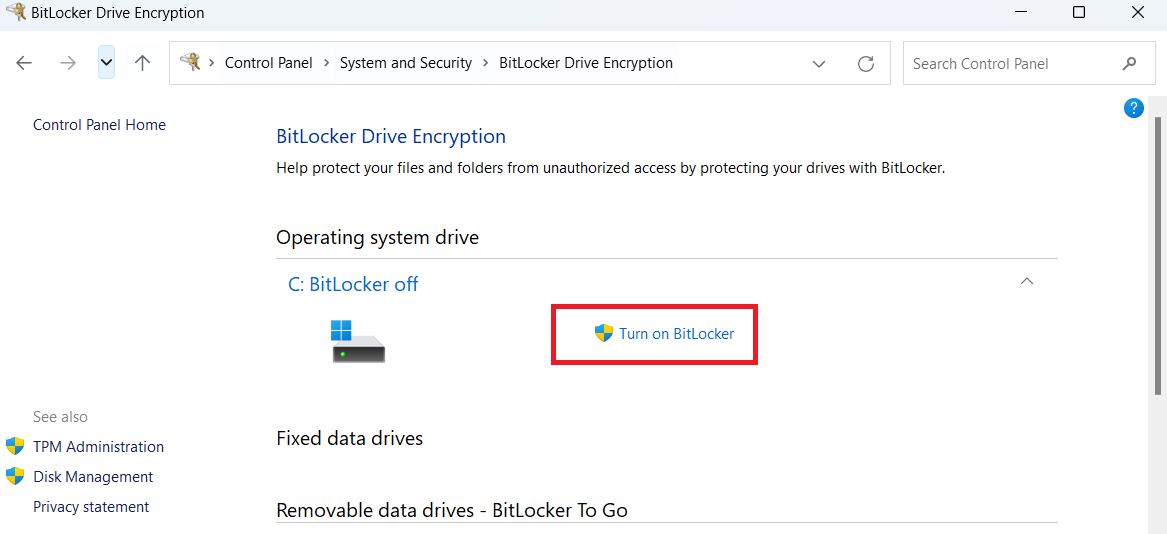
- Select the drive you want to encrypt and click on Turn on BitLocker.
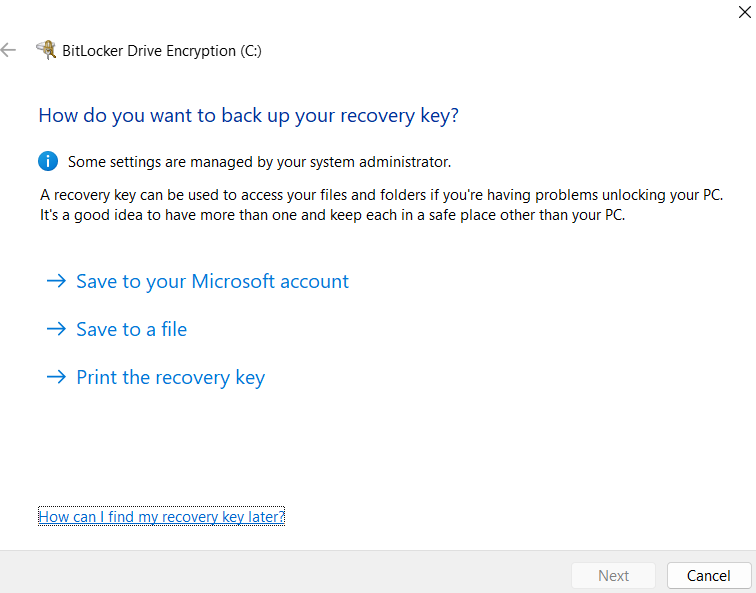
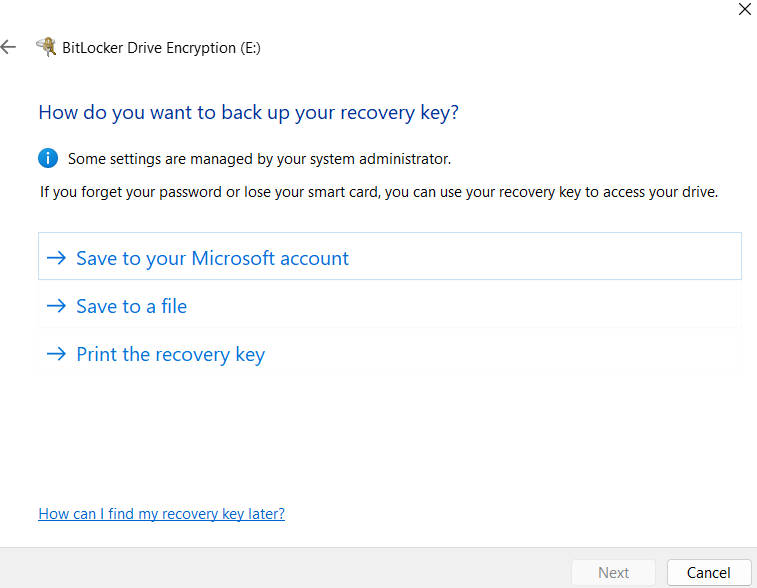
- Next, choose your preferred method to back up your recovery key.
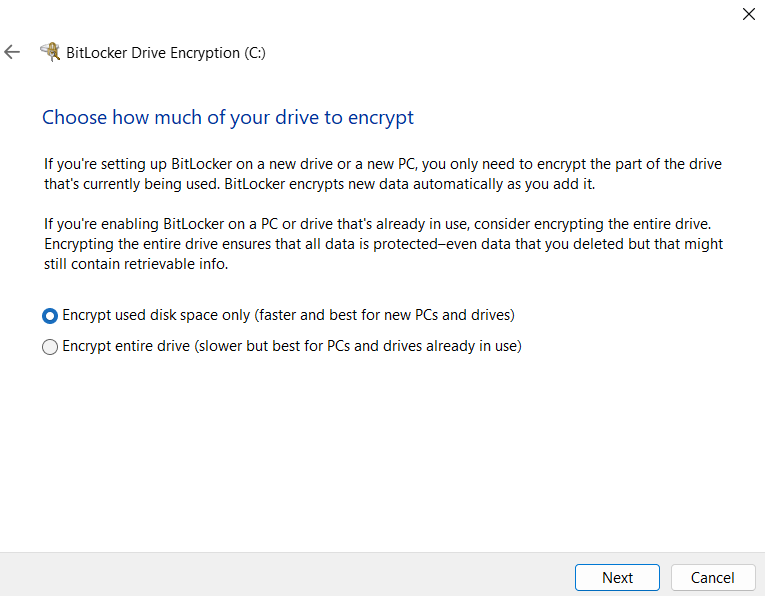
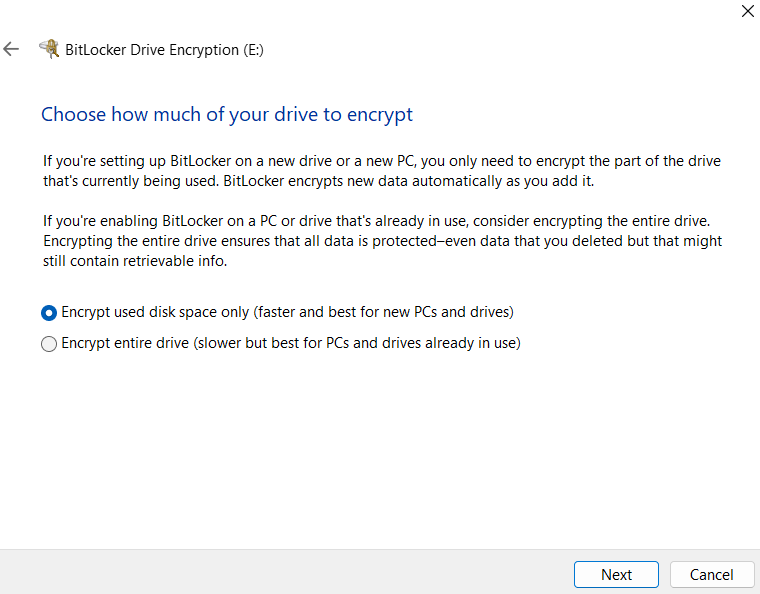
- In the next window, you’ll have to choose between Encrypt used disk space only , which is faster and ideal for new PCs and drivers. Or Encrypt entire drive , which is slower but better for computers and hard drives you’re already using. Then, click Next .
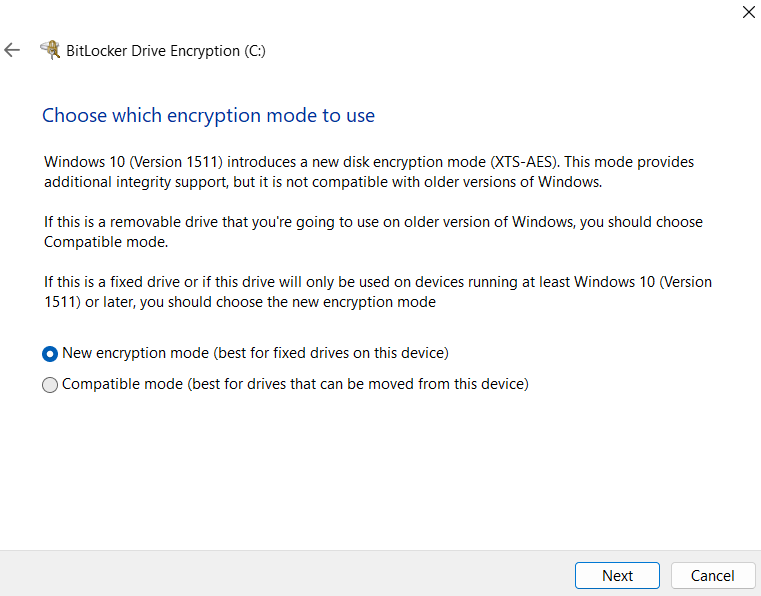
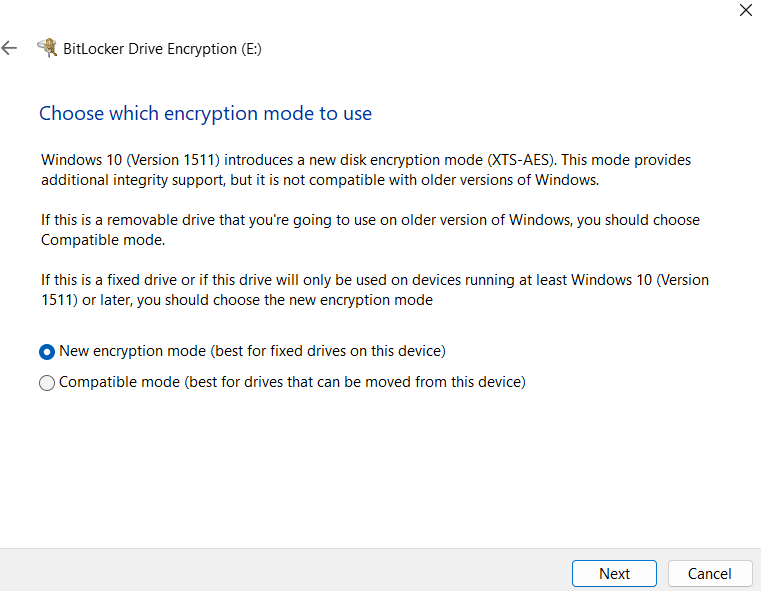
- Here, you have to choose between New encryption mode and Compatible mode and click Next .
However, if there’s a chance you’ll need to connect the drive to an older version of Windows, then go with the Compatible mode option instead. You won’t get the latest security features, but it’ll let you access the drive across different Windows versions without any headaches.
- You can start encrypting your system drive right away if you think everything is okay. However, to be on the safer side, select the Run BitLocker system check box to ensure it can read the recovery and encryption keys correctly before encoding the drive.
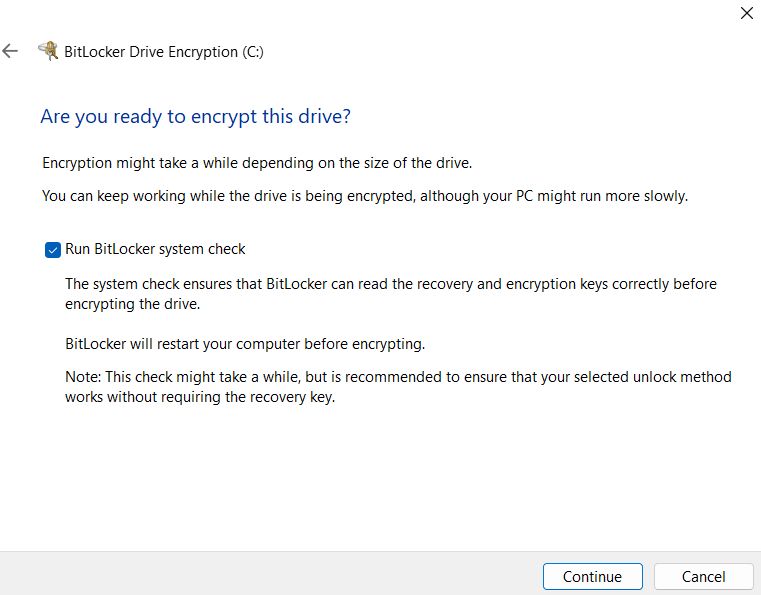
- After the check, the encryption will automatically start when you log in to your PC. Remember that your PC will be very slow, so you need to choose a time when you’re not too busy.
How to enable BitLocker encryption on removable drives Let’s go through the steps below:
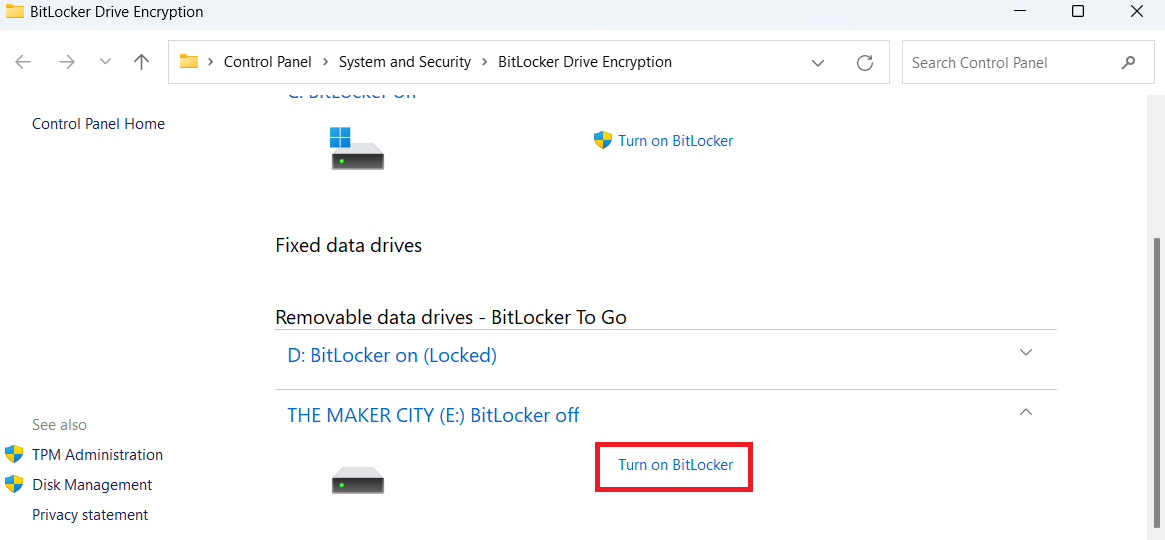
- Type “Manage BitLocker” in the search field and press Enter.
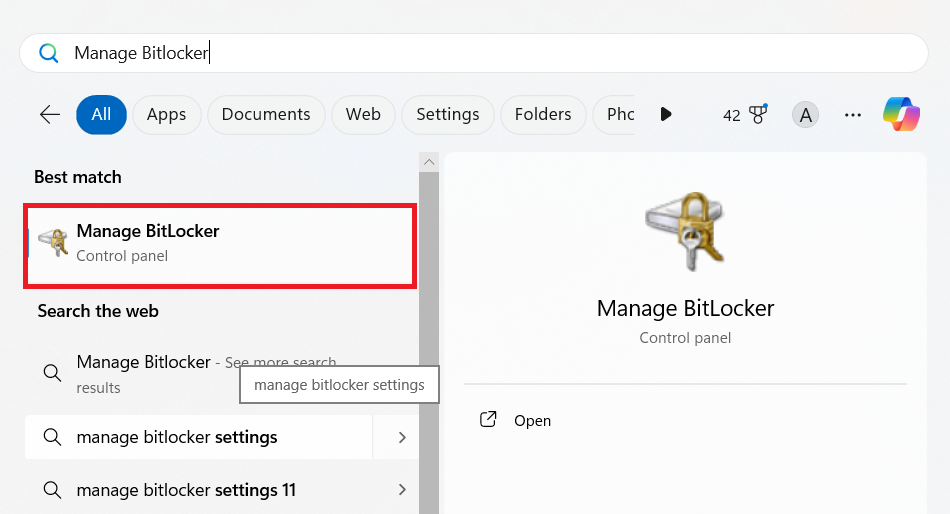
- Choose the removable drive you want to encrypt and click on Turn on BitLocker under Removable data drives – BitLocker To Go .
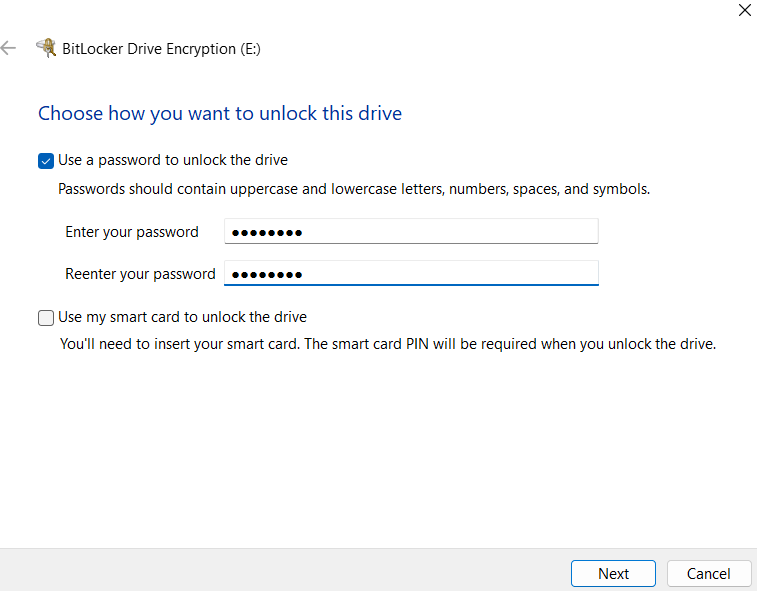
- You’ll be prompted to select how you want to unlock your drive, either via password or a smart card.
- Next, choose the backup option you want and click Next.
- Select how you want to encrypt your hard drive and select Next. You can choose between Encrypt used disk space only and Encrypt entire drive.
- Now, pick the encryption mode to use, such as New encryption mode or compatible mode.
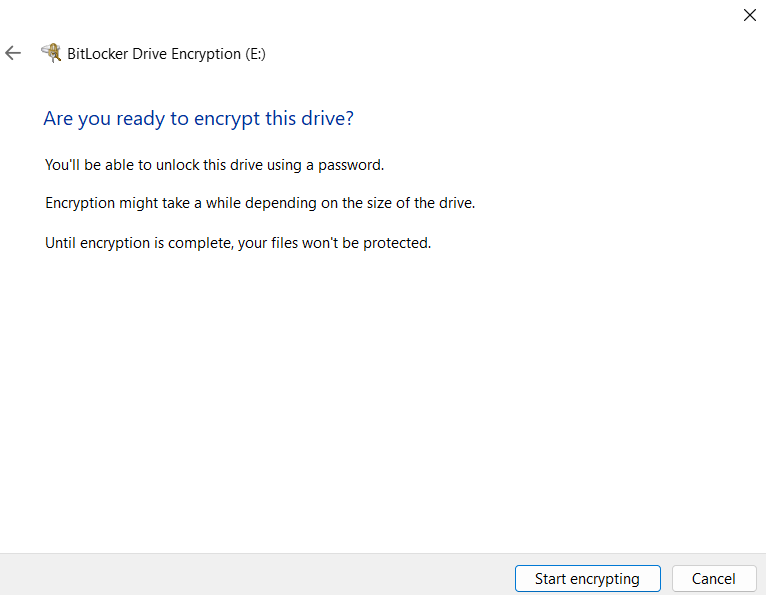
- Finally, click Start encrypting to start the process.
How to enable Windows 10 or 11 BitLocker without the TPM
If you can’t enable the TPM on your computer, you can still enable the BitLocker encryption by following the below steps:
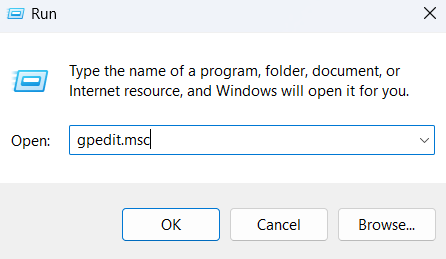
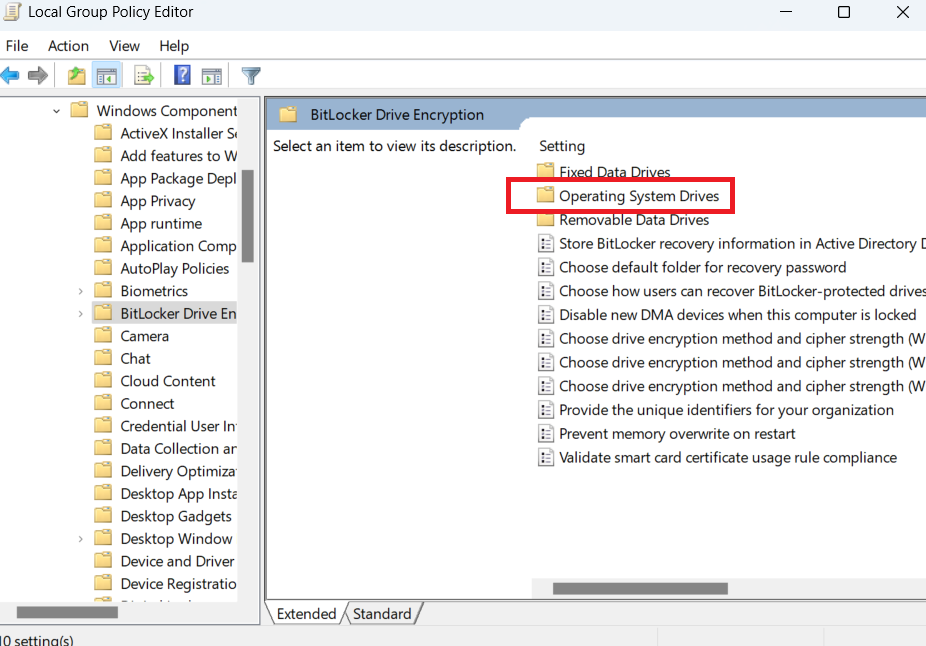
- Open the Run dialog box and type “gpedit.msc” and hit Enter.
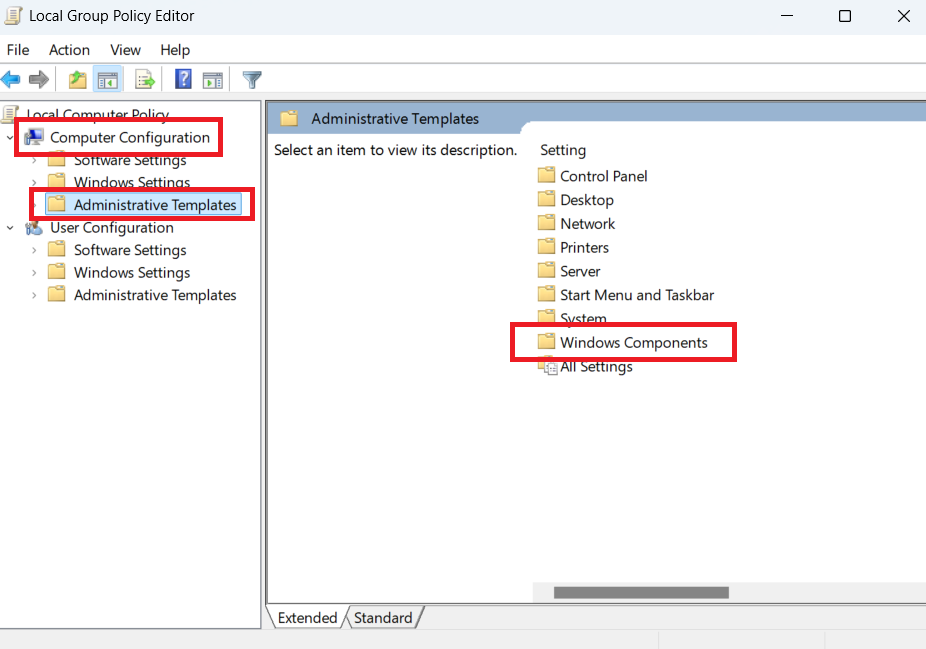
- Go to Computer Configuration , select Administrative Templates , and double-click Windows Components.
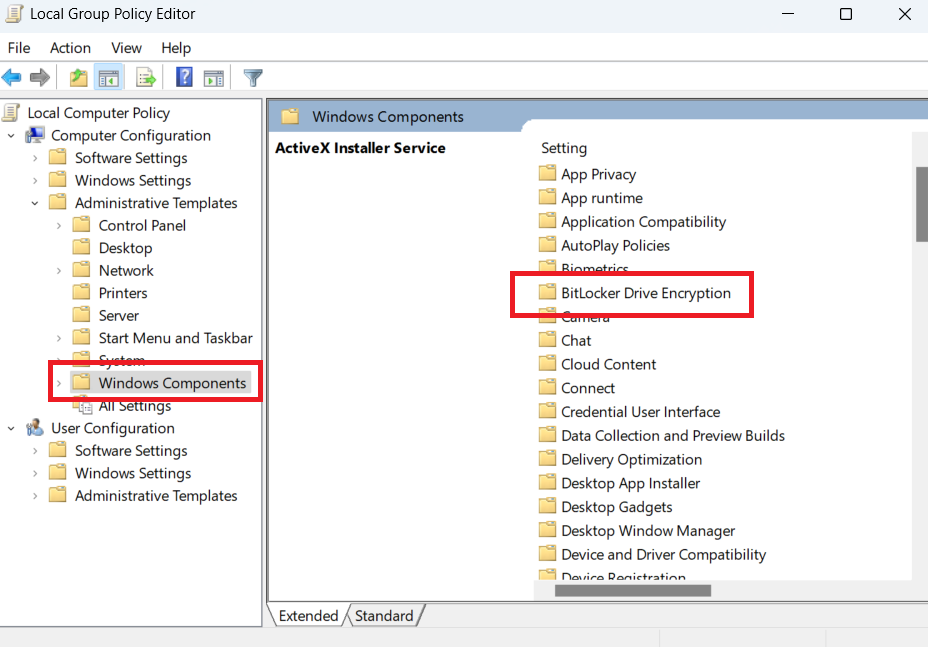
- Then double-click on BitLocker Drive Encryption.
- Go to Operating System Drives by double-clicking on it.
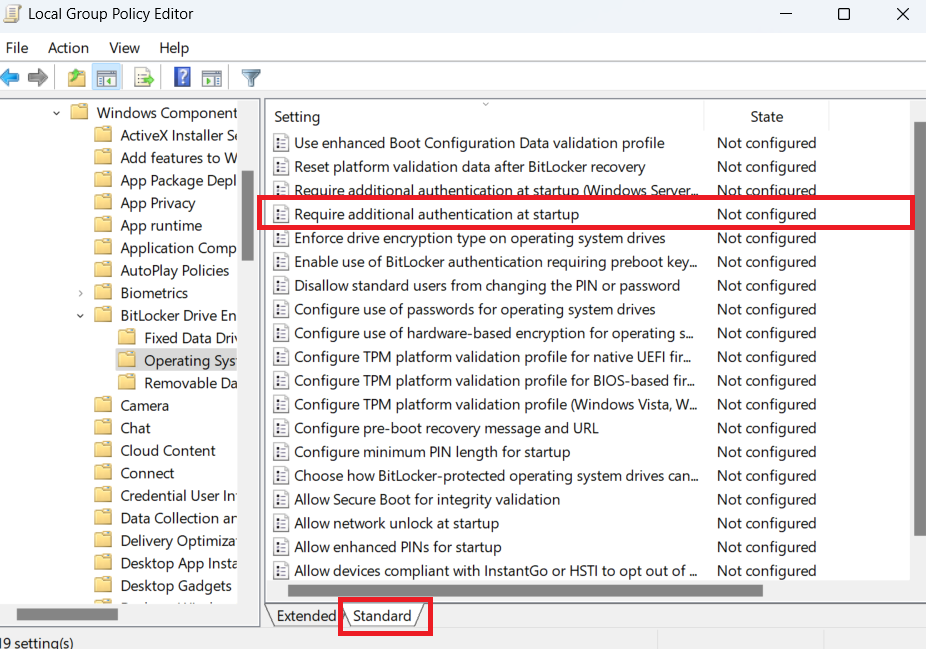
- Double-click Require additional authentication at startup. Click on the Standard button to get a clear view.
- Check the Enabled button and make sure the Allow BitLocker without a compatible TPM (requires a password or a startup key on a USB flash drive) is checked too.
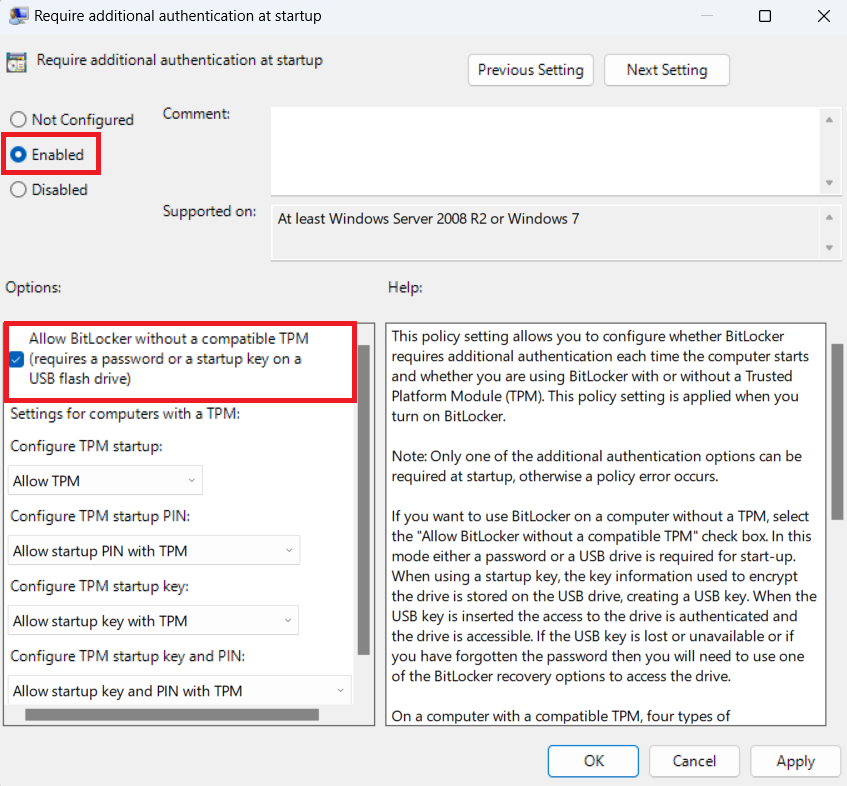
- Click Apply and select OK to complete the process.
- After that, follow the steps outlined above to enable BitLocker on your system.
How to Disable Windows BitLocker on Windows 10/11
Disabling BitLocker is quite easy. Here’s how to do it using the Control Panel:
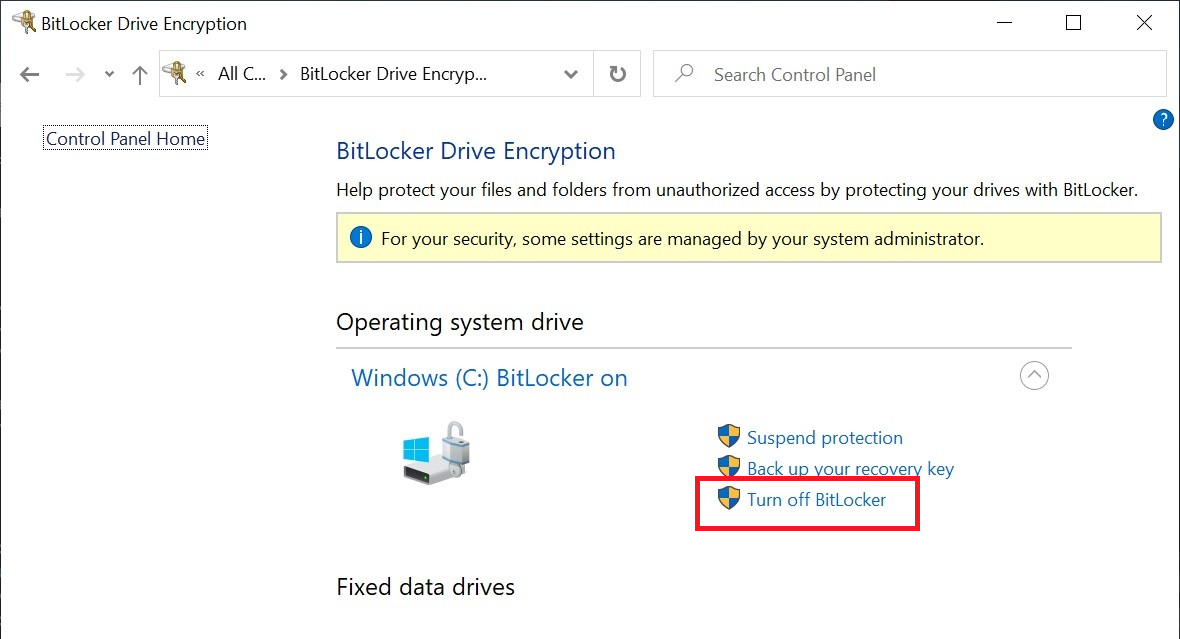
- Open the Control Panel and go to System and Security . Then, select BitLocker Drive Encryption.
- Click on Turn off BitLocker to deactivate it.
Check the options you chose when you first enabled the Bi tLocker drive encrypti on. Look into your Microsoft account online and check under Devices to see if your key is stored there.
You can also check any printed copies or USB drives might have saved it on.
📌 Here’s a detailed guide to help you: BitLocker Recovery Key: How to Avoid Losing It and What to Do if You Do
How BitLocker Encryption Compares to Other Windows Encryption Tools
In this section, I’ll discuss various Windows encryption methods and compare them with BitLocker. This will help you make an informed decision, especially if you’re keen on securing your data.
| Feature | BitLocker | Windows Device Encryption | EFS | VeraCrypt | 7-Zip |
|---|---|---|---|---|---|
| Encryption level | Full-disk | Full-disk | File-level | Full-disk, file, and folder | File-level (within archives) |
| Availability | Pro, Enterprise, Education | Some Home, Pro (TPM needed) | Pro, Enterprise | Any Windows version | Any Windows version |
| Cost | Free | Free | Free | Free | Free |
| Security level | High | Moderate to high | Moderate | High | Moderate |
| Ease of use | Easy | Easy | Moderate | Moderate to complex | Easy |
| Compatible with external drives | Yes (Pro, Enterprise) | Limited | No | Yes | Yes |
| File-level encryption | No | No | Yes | Yes | Yes |
| Cross-platform | No | No | No | Yes | Yes |
| TPM requirement | Yes (recommended) | Yes (mandatory) | No | No | No |
1. Windows Device Encryption
This encryption tool is a lighter version of BitLocker that uses XTS-AES. It’s a perfect solution for everyday users who want to keep their personal information safe without worrying about complex security settings. Device Encryption is turned on by default when you first sign in or set up a device with a Microsoft account, school, or work account. However, you’ll have to manually turn this feature on if you use a local account.
- Available on more Windows editions if the PC has the TPM and meets Modern Standby requirements
- Fully integrated with Windows
- Limited to Windows Pro, Enterprise, and Education editions
- Available on only compatible devices
- Lacks file-level encryption options
2. EFS (Encrypting File System)
EFS is another Windows encryption built-in tool that focuses on encrypting files and folders. It’s available on Pro and Enterprise editions. However, unlike BitLock, EFS allows you to encode individual files and folders instead of entire drives.
- Provides flexible file- or folder-level encryption
- Encryption keys are tied to user accounts
- Can encrypt files on remove servers or network servers
- Only available on Pro and Enterprise editions
- Not as secure as BitLocker since it doesn’t encrypt the entire drive
- Requires extra setup for recovery keys, which aren’t stored in a Microsoft account
- Only works on the NTFS file system
3. VeraCrypt
VeraCrypt is a free, open-source encryption tool that offers robust encryption for individual files, folders, and full disks. You can easily customize it for Windows, macOS, and even Linux.
- Free and has a strong reputation for security
- Can encrypt data on a file-level, folder-level, and supports full-disk encryption
- Works on external drives and removable media
- Requires a separate installation since it’s not integrated with Windows
- Can be less user-friendly
- Setup and recovery can be complex, particularly for beginners
- No official support, and updates rely on its open-source community
4. 7-Zip
7-Zip is a free file compression tool that also provides encryption for files within compressed archives. It doesn’t support full-disk encryption, but it offers a quick way to protect files.
- Free and very lightweight
- Can easily access encryption for individual files
- Offers AES-256 encryption for compressed files
- Only encrypts files in archives
- Not a full-disk encryption tool and won’t secure data outside of compressed files
- Requires manual password input each time you open an encrypted file
- Limited to file-level encryption
- Lacks integration with the Windows OS
So, all in all, if you want to encrypt your entire drive, I’d recommend BitLocker because it’s the most secure and convenient choice. Better yet, you can also enable Device Encryption together with BitLocker.
Common Concerns Users Have with BitLocker Encryption and How to Fix Them
Some users have concerns about Windows BitLocker. We’ve already covered some of the issues, but here are some general concerns and how to deal with them:
1. Privacy concerns
Privacy is a hot topic now because of the many technologies and AI stuff coming out. So it has become more crucial to secure your privacy online . But it’s also important to secure the data on your PC. So, your concerns are understandable.
Some people don’t trust Microsoft, and by extension, BitLocker. Some are even concerned about the security of the BitLocker recovery key. If you’re one of them, you could keep your recovery key on your USB instead of your Microsoft account.
If you don’t trust Microsoft, you could use other encryption tools we’ve discussed. But I think it’s safer with Microsoft than with a tool managed by a community forum. After all, there are regulatory bodies keeping watch on the company.
2. Compatibility issues
If your Windows version doesn’t support BitLocker, you may have to upgrade. However, if you don’t want to, there are third-party tools too. If you’re using Windows 10 or 11, try using Device Encryption. If BitLocker encryption isn’t working on your Windows 10 or 11, there is an issue preventing it from activating. You can:
- Check the hardware requirements if you’re using TPM 1.2 or higher, like we’ve already discussed.
- Check if the Group Policy settings are correctly configured. To do that, open the Group Policy Editor, then go to Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption . There, check if the status of relevant policies are correct. For example, look for settings like Choose drive encryption method and cipher strength and Require additional authentication at startup in the Operating System Drives folder.
- Update your Windows or firmware. It may fix the problem.
3. Performance concerns
BitLocker shouldn’t affect your computer’s performance, especially if you’re using Windows 10 or 11 or an SSD. However, some tests have been conducted that suggest otherwise.
Anyway, if you’re absolutely sure that every time you enable BitLocker you notice a performance dip, first check if you meet the recommended specs for encryption. And try updating your hardware if necessary.
Alternatively, you can encrypt only the necessary data instead of the entire disk or just disable BitLocker altogether.
Best Practices of BitLocker Encryption for Online Safety
Here are some best practices to consider when using BitLocker encryption to ensure optimal online security:
- Choose a strong, unique password for unlocking your BitLocker-protected drive. Consider using a combination of uppercase and lowercase letters, numbers, and special characters.
- If your computer has the TPM, enable and use it for added security.
- Keep your operating system and BitLocker software up to date with the latest security patches to address any vulnerabilities.
- Store your BitLocker recovery key in a safe and separate location, preferably offline. And don’t store it on the same device you’re encrypting.
- Use Secure Boot in combination with BitLocker to ensure that only authorized and trusted software can boot your system.
- Even with encryption, data loss can still occur due to various reasons, like hardware failure, malware, or software issues. So, regularly back up your important data to an external source or cloud storage.
- Use genuine hardware and software to avoid potential security risks posed by counterfeit products.
- Keep your BitLocker password and recovery key confidential. Avoid sharing them with anyone unless necessary.
- If you’re donating or selling your computer, make sure to securely wipe the drive using proper methods to remove any residual data.
- Set your BitLocker drive to automatically lock after a certain period of inactivity for additional protection.
- Periodically review and update your BitLocker encryption settings as needed to adapt to changes in your environment.
Protect Your Data with BitLocker Drive Encryption: Final Thoughts
Windows BitLocker may not be for everyone. I’m personally more concerned about my privacy and security online because I don’t keep sensitive data on my PC. However, I’ve encrypted my external drive with BitLocker.
I understand my PC could get stolen, damaged, or just give up for whatever reason. So getting access to my data at all times is crucial for me, and BitLocker accomplishes only one of them. But that’s me.
Find out what works for you and take the appropriate action. If you have any questions, let us know in the comments below.
![[Complete Guide] How to Enable and Use BitLocker Drive Encryption on Windows 10/11](https://www.auslogics.com/en/articles/wp-content/uploads/2024/12/Complete-Guide-How-to-Enable-and-Use-BitLocker-Drive-Encryption-on-Windows-1011-568x359.webp)