- What Is Malware?
- Common Types of Malware
- What Are the Common Points of Entry?
- How Can I Know If I Already Have Malware?
- How to Prevent Malware From Taking Over Your System
- 1. Keep Your Operating System Updated
- 2. Install and Regularly Update Anti-Virus Software
- 3. Use a Firewall to Block Unwanted Connections
- 4. Avoid Clicking on Unfamiliar Links or Attachments
- 5. Be Careful About Downloading Software
- 6. Don’t Use Unsecured Networks
- 7. Back-Up Your Data Regularly
- 8. Enable Two-Factor Authentication (2FA)
- 9. Strengthen Your Passwords
- 10. Educate Yourself on Cybersecurity Best Practices
- Wrap Up
- FAQ
In 2022, over 5 billion malware attacks were detected worldwide, with the major types of malware being worms, ransomware, viruses, and trojans. According to the data by Statista, email and websites were the two main attack vectors. According to AV-TEST, an independent IT security institute, over 450,000 new malicious programs are detected every day. To date, there are over 1.2 billion total malware and potentially unwanted programs (PUA) in existence. This scary trend makes it more crucial than ever to protect your system from potential malware threats. By implementing proactive measures, you can stay safe and protect your confidential data from malicious actors. In this post, we’ll talk about malware detection and how to prevent malware and safeguard your digital world.
What Is Malware?
Malware, short for “malicious software,” is designed to exploit or cause harm to applications, devices, services, or networks. This threat can come in many forms, such as worms, viruses, ransomware, Trojans, and spyware.
There are various ways to tell if your computer is infected by malware.
Some of the symptoms include your computer becoming slower than usual, startup or shutdown problems with your device, or annoying pop-ups when you open a new browser window.
Once installed, malware can:
- Monitor your activities – Malware can log what you are doing on your devices, such as keystrokes or mouse clicks. It can also capture your personal information, online credentials, or financial details.
- Hijack your device – Malware can use your device to infect other devices in the network.
- Damage or disable your device – Malware can cause your device to malfunction, leading to startup errors, sudden shutdowns, or software crashes.
Cybercriminals often use malware to capture or steal data from their victims and use the stolen data. These data usually contain confidential information such as passwords, financial records, healthcare information, or other personal details.
Almost all industries have fallen victim to malware in the US, including organizations from the healthcare, education, and financial sectors.
Ransomware attacks caused an estimated $11.5 billion in global damages in 2019 and $20 billion in 2020.
Common Types of Malware
VirusesThese malicious programs attach themselves to clean files and replicate when the infected file is executed, spreading to other files and systems. Viruses can steal, corrupt, or delete data, causing significant harm to the infected computer. The Zeus virus is a common virus that was detected in 2006 and is still a threat today. WormsUnlike viruses, worms can spread independently, often through network vulnerabilities, without the need for user action. Once it gets inside a system, it self-replicates and looks for networked devices to attack. Worms are usually disguised as legitimate files, often going unnoticed by users. WannaCry, which is also a form of ransomware, is one of the well-known worm attacks that spread across a number of computer networks like a bushfire in May 2017. The malware encrypted files on users’ PCs, making them impossible to access. The attackers then demanded ransom payments in Bitcoin to decrypt them. TrojansDisguised as legitimate software, Trojans trick users into downloading and installing them, providing unauthorized access to the attacker. Once inside the system, the Trojan’s malicious code – or payload – is installed, facilitating the exploit. Trojan horses give attackers backdoor access to devices, where they can install viruses or worms, perform keylogging or steal data. RansomwareThis type of malware encrypts your files and demands a ransom in exchange for the decryption key. It’s one of the most profitable types of malware used by cybercriminals, leading to significant financial losses and data breaches. The U.S. experiences the highest cost of data breaches averaging $9.44m, according to IBM Data Breach Report 2022.SpywareSpyware secretly monitors and collects information about your online activities without your consent. It can capture sensitive details like your browsing habits, login credentials, and credit card details. AdwareAdware displays unwanted advertisements, often in the form of pop-ups, and can redirect you to malicious websites. While the least destructive type of malware, adware can still be highly irritating and pose risks to your online security. RootkitsRootkits provide unauthorized access to a computer while hiding their presence from the user and security software. This sophisticated malware isn’t easily detectable and can be challenging to remove. KeyloggersKeyloggers record your keystrokes, enabling attackers to capture sensitive information like passwords and credit card details. They are termed surveillance malware due to their spying nature, enabling perpetrators to obtain users’ usernames and passwords without their knowledge or consent.
What Are the Common Points of Entry?
Email Attachments
Email attachments can be dangerous as they may contain viruses disguised as legitimate files, infecting the user’s computer when downloaded and installed unknowingly. Phishing attacks, a common method of delivering malware via email, involve attackers posing as legitimate entities to trick victims into revealing sensitive information like credit card details or social security numbers, leading to potential financial and identity theft.
Drive-By Downloads
In some cases, you can download legitimate software from a compromised website without knowing it. Attackers use this tactic to inject malware into your device when you access those sites and click on a link. In authorized downloads, the file or app to be downloaded may be legitimate but may have been compromised by the attacker. That file is then used as a vector to deliver the malware.
Infected USB Devices
Due to USB drives’ portability and ease of access, criminals often use them to spread malware. When a user plugs the malware-infected flash drive into a computer, the malware downloads itself into the computer. This can happen either automatically or when the user clicks on an infected file. The malware gives the attacker access to the computer, allowing them to download confidential information.
Peer-to-Peer File Sharing
Peer-to-peer (P2P) file sharing is a popular method of distributing files and data over the internet. Unlike traditional file distribution methods, which involve a central server hosting the files, P2P file sharing allows users to exchange files with one another directly. This decentralized approach has both advantages and potential risks. While it facilitates faster downloads and reduced bandwidth cost, it can be a breeding ground for distributing malware, as users inadvertently download infected files from untrusted sources.
How Can I Know If I Already Have Malware?
You might be wondering , what’s a possible sign of malware? Well, no matter the type of malware, here are some common indicators that may suggest the presence of malware in your computer: Slow performance. If your computer suddenly becomes sluggish, takes longer to start up, or experiences frequent crashes, it could be a sign of malware. Malicious software often consumes system resources, leading to decreased performance. Unexpected pop-ups: If you notice an increase in pop-up ads, especially ones that appear even when you’re not browsing the internet, it could be a sign of adware or other malware. Unusual network activity: If your internet data usage has significantly increased without any apparent reason, it could indicate that malware is using your network to communicate with external servers. Disabled security software: Malware often attempts to disable or bypass antivirus or firewall software to avoid detection. If you find that your security software has been turned off without your knowledge or is unable to update, it could be a sign of malware interference. Unauthorized changes: If you notice new browser toolbars, unfamiliar icons on your desktop, or changes to your browser’s homepage or search engine settings, it could be a sign of malware. Unexpected system behavior: Malware can cause various unusual behaviors, such as files or folders disappearing, new programs appearing without your consent, or your web browser redirecting you to unfamiliar websites. Unauthorized access: Unexplained logins or activities in your online accounts might indicate a security breach.
Also Read: Signs of Malware: How to Know if Your Computer is Infected
How to Prevent Malware From Taking Over Your System
It’s said prevention is better than cure and for malware attacks, it stands true. If you suspect malware on your computer or want to fortify your digital defenses, here are effective strategies on how to prevent malware :
1. Keep Your Operating System Updated
One of the most crucial steps in preventing malware infections is keeping your software up to date. Software updates often include security patches that address vulnerabilities exploited by malware.
Enable automatic updates for your operating system, applications, and plugins. If automatic updates are not available, make it a habit to regularly check for updates manually.
Neglecting updates can leave your computer exposed to known security flaws, making it an easy target for malware attacks.
Also Read: How to Keep Your Software Up To Date?
2. Install and Regularly Update Anti-Virus Software
Having robust anti-virus software is essential if you want to significantly reduce the risk of falling victim to these threats.
An anti-malware tool is what protects your computer so that it doesn’t get a computer virus . One such tool is Auslogics Anti-Malware, a trusted and reliable malware detection and removal tool.
The software thoroughly scans your entire system, checking system memory, temporary folders, and the safety of auto-start programs, as well as detecting cookies that track your online activity. It then quarantines and gets rid of them.
To use Auslogics Anti-Malware:
- Go to Auslogics’ official download page and install the program.
- Once installed, the malware removal tool will update its database to ensure you’re protected from the latest threats.
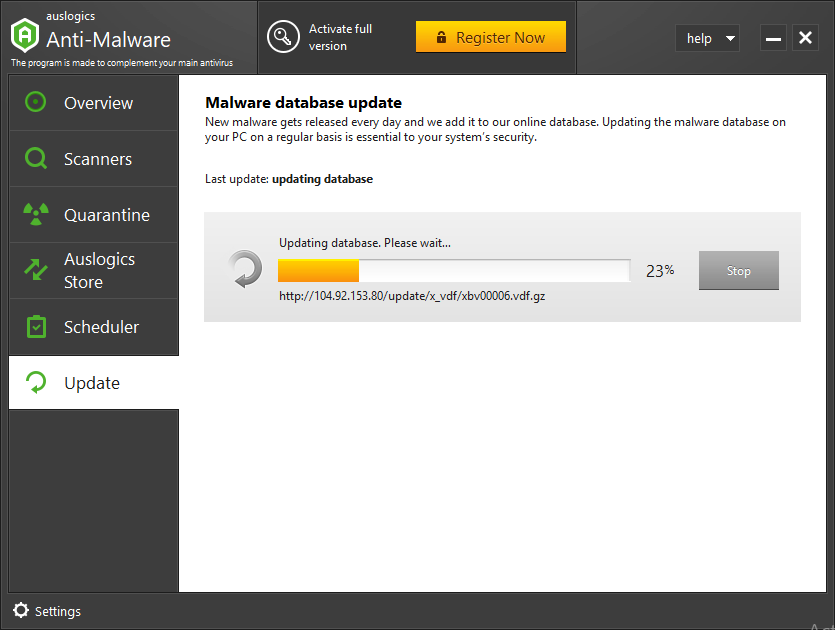
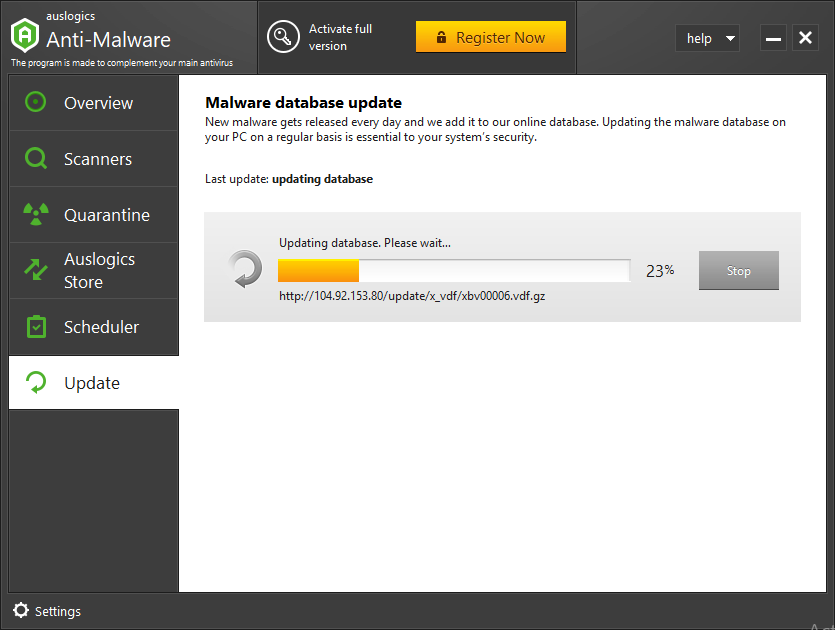
- Select your preferred option and hit the Start Scan button.
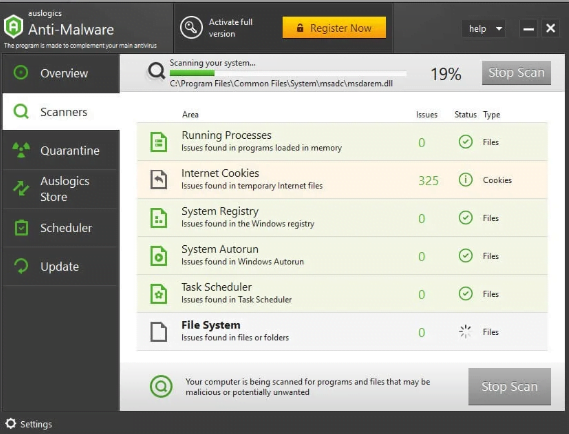
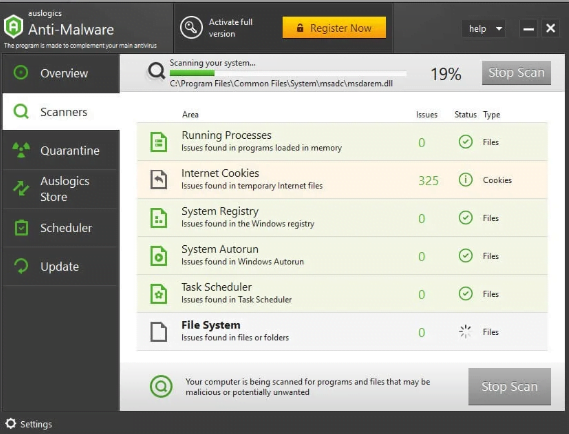
- The tool scans for potential malware and provides a detailed overview of the threats detected. Note that you’ll need to upgrade to the Pro version to get rid of the viruses.
Auslogics Anti-Malware even lets you schedule regular automatic scans to catch any malware that might have gotten into your system undetected.
Also Read: Auslogics Anti-Malware: Features and Reviews
3. Use a Firewall to Block Unwanted Connections
A firewall acts as a barrier between your computer and the internet, monitoring incoming and outgoing network traffic and determining whether to allow or block it based on a set of predetermined rules.
By setting up a firewall, you can prevent unauthorized connections from accessing your system. Most modern operating systems come with built-in firewalls, but they may not be activated by default.
Hence, it’s essential to check your firewall settings and ensure that it’s turned on. Additionally, review and adjust the firewall rules to match your specific security requirements.
On Windows 10, you can easily check if the firewall is enabled. To do so:
- Press with Windows Key, type “ Control Panel” and hit Enter.
- Select System and Security > Windows Defender Firewall.
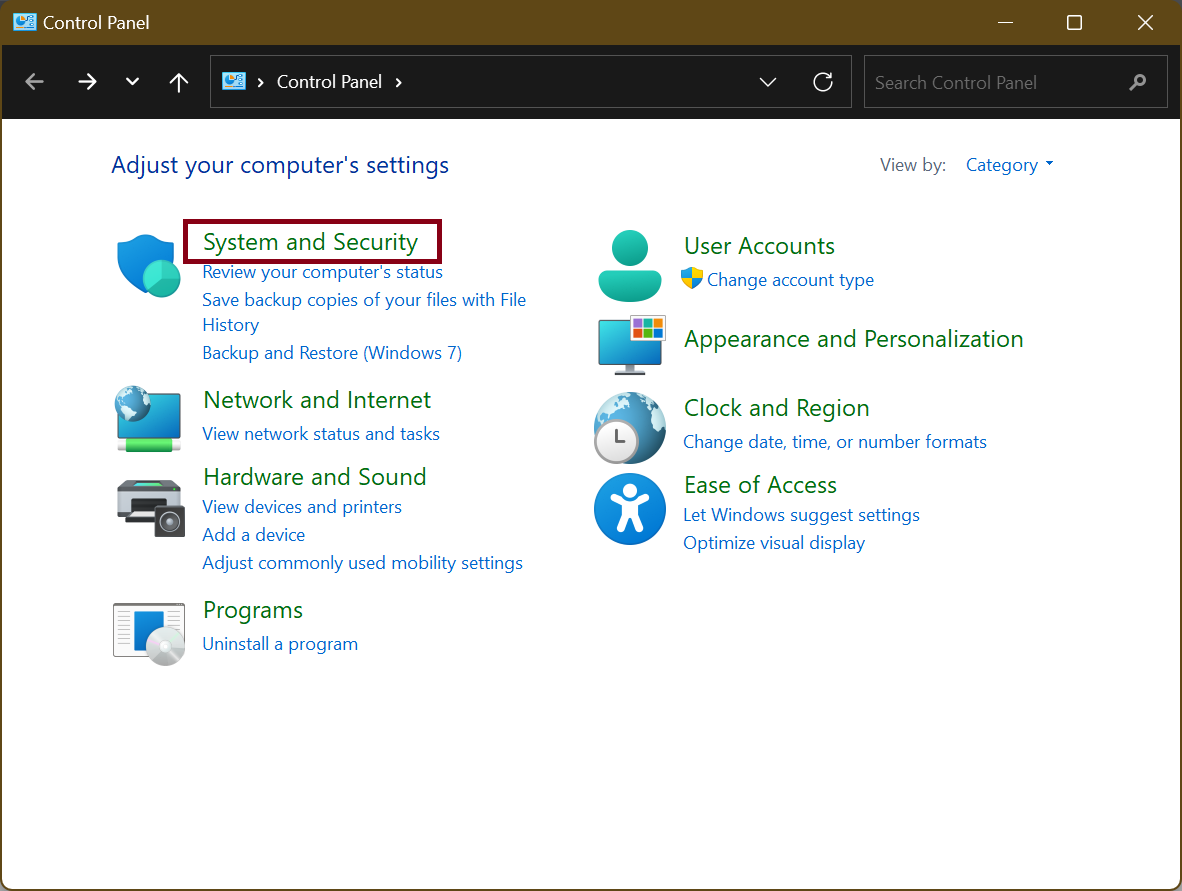
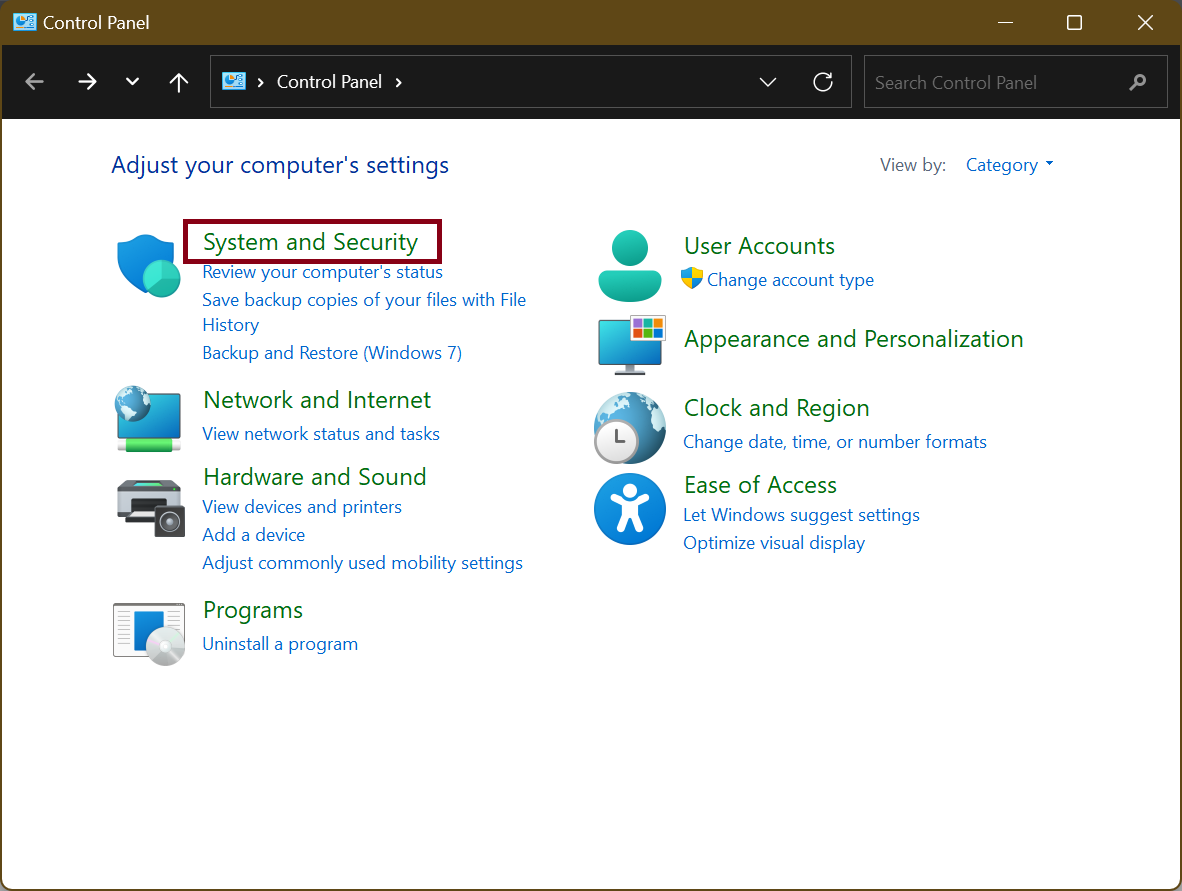
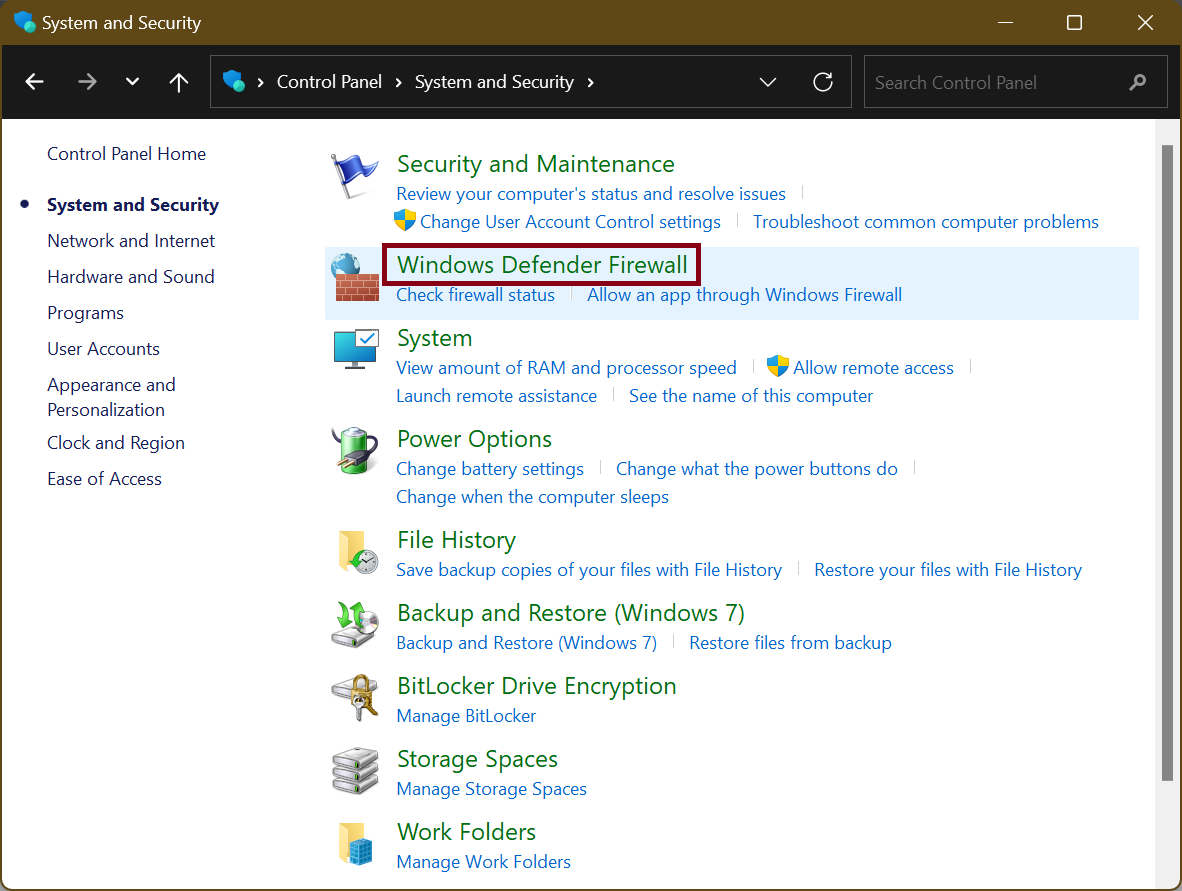
- Check if the option that says Windows Defender Firewall State is marked On.
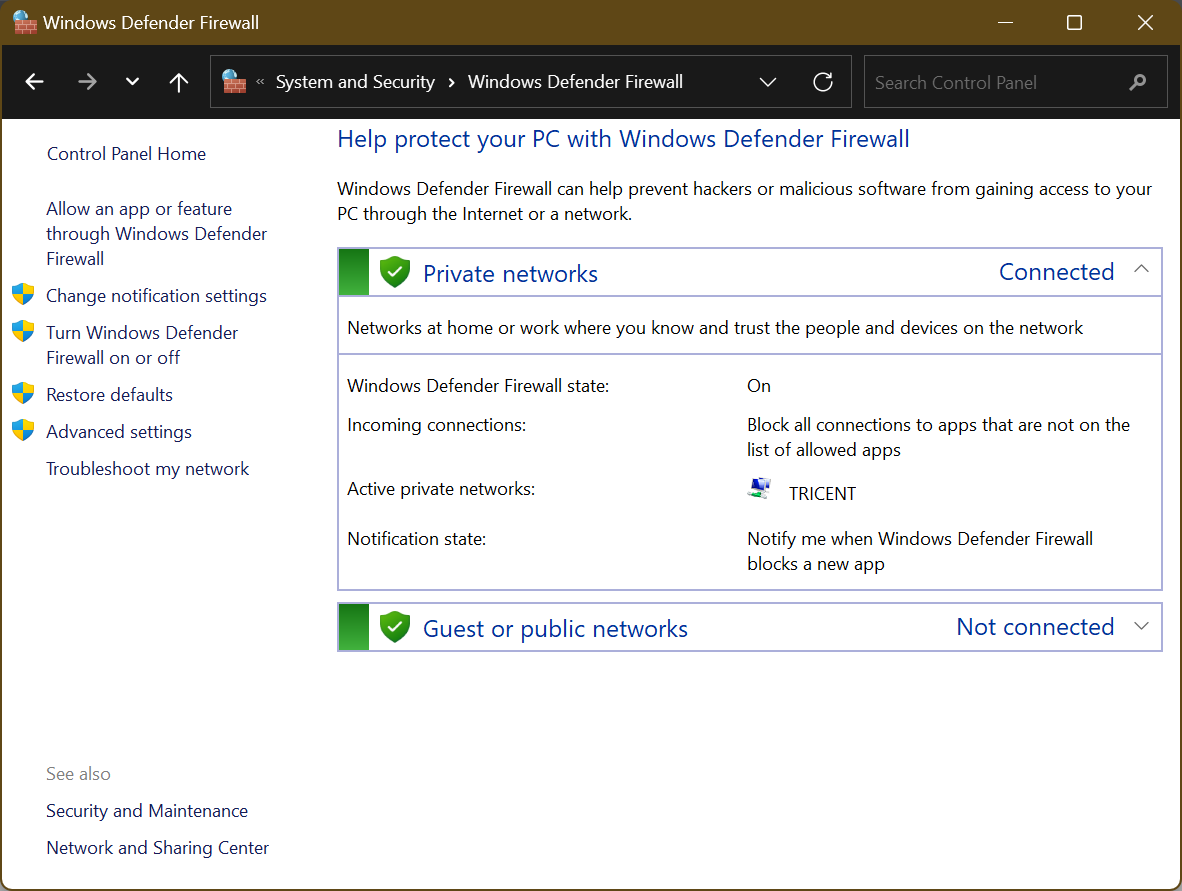
- If disabled, turn it on by selecting Turn Windows Defender Firewall on or off in the left pane.
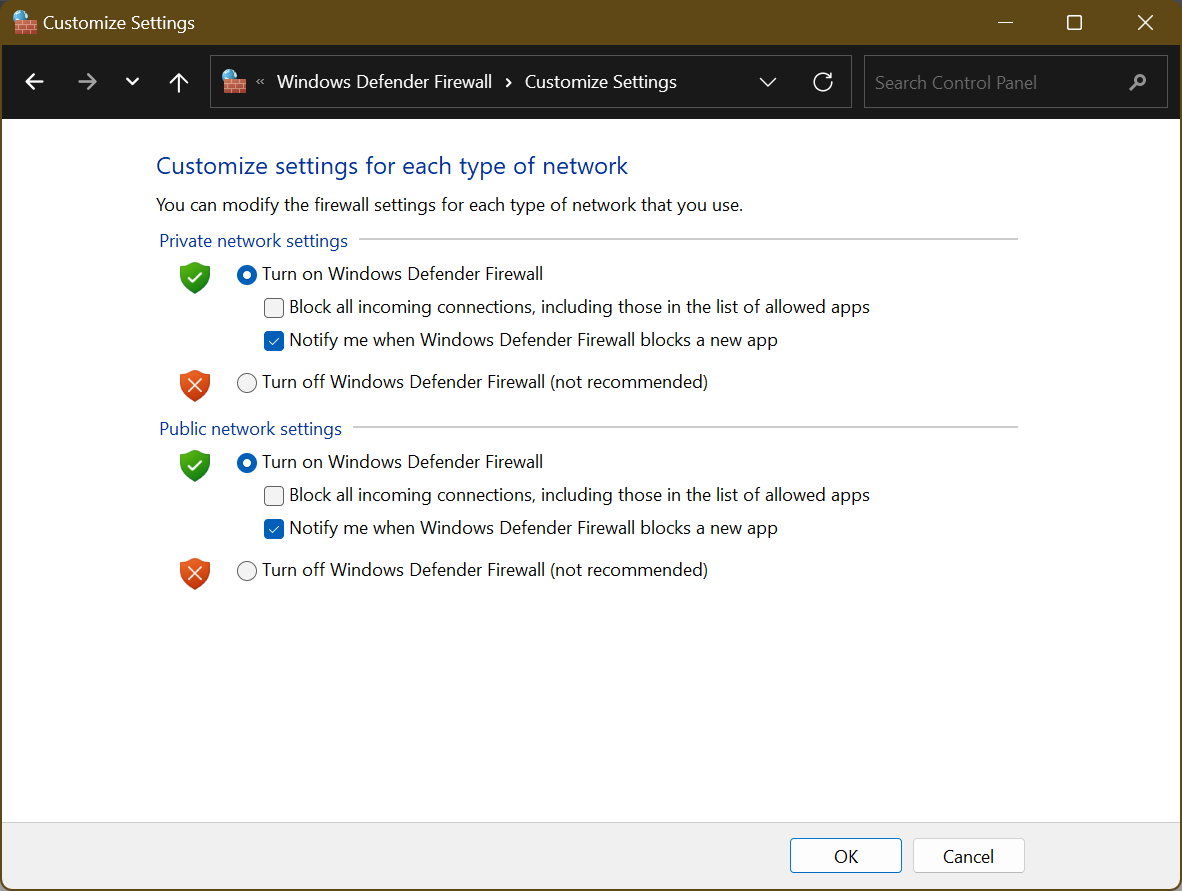
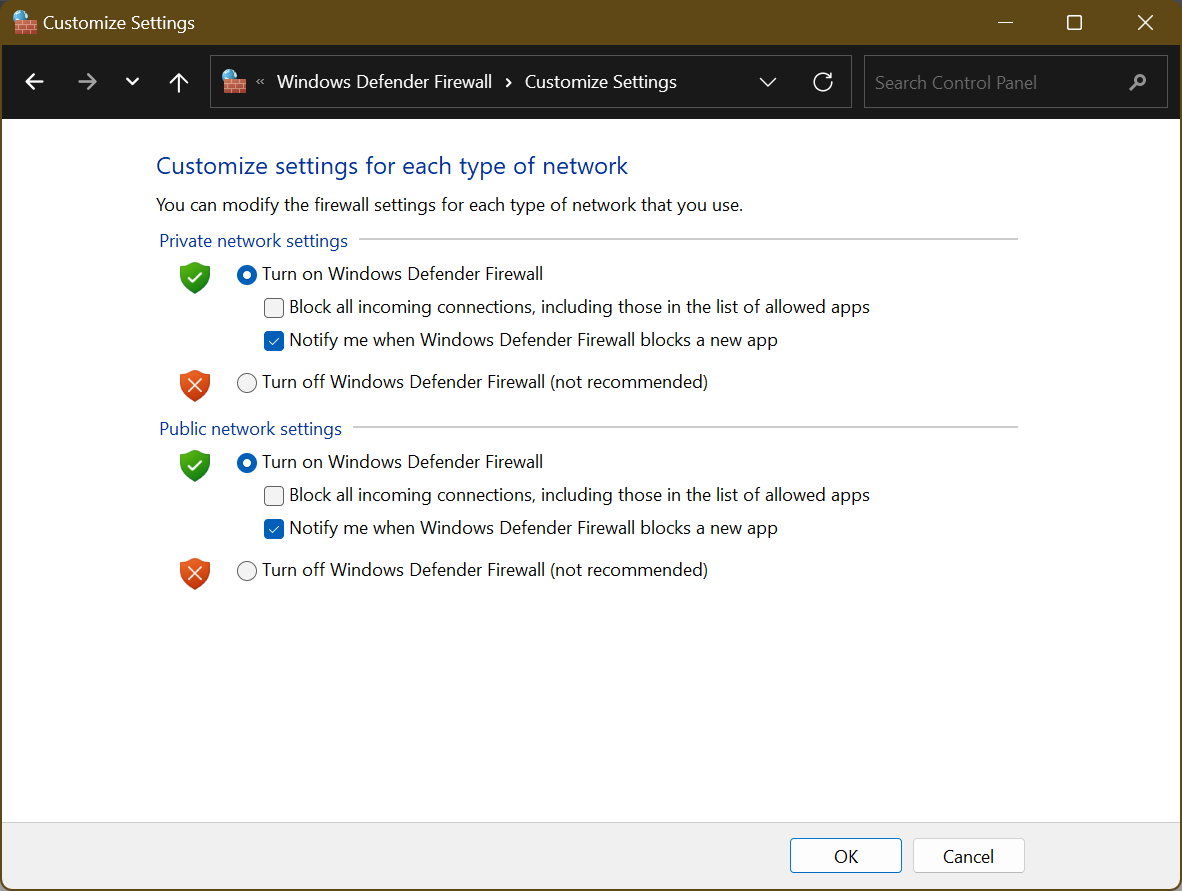
- In the Customize settings for each type of network window, select Turn on Windows Defender Firewall for both private and public network settings, and click OK.
While firewalls are an essential part of your computer’s security, they are not a foolproof solution. Consider adopting a multi-layered approach by installing anti-malware, regularly updating your system, and leveraging safe browsing practices.
4. Avoid Clicking on Unfamiliar Links or Attachments
One common way malware enters your system is through email attachments or suspicious links. Most email providers have spam filters that can analyze the contents of the email and determine if the email has malware.
However, there can be times when legitimate emails also get tagged, or malicious emails still get through, which is why you may need to check some of those emails manually.
Be sure to carefully examine the sender’s email address. Cybercriminals often use email addresses that resemble legitimate ones, but upon closer inspection, you may notice slight variations or misspellings.
Suppose the email address does not appear to have a legitimate domain (e.g., nameofbank@gmail.com instead of customerservice@nameofbank.com). In that case, the email may be a phishing scam and you shouldn’t attempt to open it or click any attachments.
If the content seems too good to be true or raises any doubts, it’s better to err on the side of caution and delete the message altogether.
Also Read: Digital Privacy: Tips on How to Protect Yourself on the Internet
5. Be Careful About Downloading Software
Downloading software from reputable sources is crucial to avoid inadvertently installing malware. Stick to official websites and trusted app stores when obtaining applications or updating existing ones.
Avoid downloading software from unverified sources, as they may contain hidden malware or other security risks. Always double-check the reliability and legitimacy of the software provider before initiating any downloads.
6. Don’t Use Unsecured Networks
Public Wi-Fi networks can be convenient, but they also pose significant risks. When connected to an unsecured network, your data becomes vulnerable to eavesdropping and malicious attacks.
To prevent exposing your system to attackers, avoid accessing sensitive information or conducting online transactions while connected to public Wi-Fi. If necessary, use a virtual private network (VPN) to create a secure connection and protect your data from prying eyes.
And, when using your Wi-Fi network, make sure it’s secured. Use strong encryption protocols, such as WPA2 or WPA3 to prevent unauthorized access.
Also Read: How to Choose VPN: Best Free VPN for Windows 10 PC
7. Back-Up Your Data Regularly
Even with robust security measures in place, it’s essential to prepare for the worst-case scenario. Regularly backing up your data safeguards it against potential loss or corruption caused by malware attacks.
In case your computer system gets compromised, you can restore your system to a clean state without losing your valuable data.
You can back up to external hard drives, cloud storage, or both to store your backups securely. If you’re a Windows 10 user, here’s a guide on Windows 10 backup and restore.
8. Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security by requiring users to verify their identity using two different methods. In addition to entering a password, 2FA typically involves providing a unique code sent to a trusted device or email.
Enabling 2FA on your important accounts, such as email and banking, significantly reduces the risk of unauthorized access and helps mitigate the impact of potential malware attacks.
Also Read: Ultimate Guide: How to Turn Off Two-Factor Authentication?
9. Strengthen Your Passwords
Weak passwords make it easier for cybercriminals to gain unauthorized access to your accounts and compromise your system. When creating passwords, opt for complexity and avoid using easily guessable information, such as common words, sequential numbers, or birthdates.
Instead, formulate passwords that combine uppercase and lowercase numbers, special characters, and numbers. A mix of these elements creates a complex password that makes it more challenging for malicious actors to crack.
It’s also advisable to consider the length of your password. The longer the password, the harder it is for cybercriminals to execute brute-force attacks.
Also read: Stay Safe Online: The Best Ways to Store Passwords
10. Educate Yourself on Cybersecurity Best Practices
Knowledge is a powerful weapon against malware. Stay informed about the latest cybersecurity threats and trends. Educate yourself and your team on the best practices for safe browsing, email hygiene, and general online security.
By fostering a culture of cybersecurity awareness, you create an added layer of protection against malware attacks.
Related: How to Remove Virus and Other Malware from Windows
Wrap Up
Malware detection and prevention requires a proactive approach to safeguard your digital environment. By implementing strategies like keeping your software updated, strengthening your passwords, and being cautious with emails and websites, you can significantly reduce the risk of malware compromising your system.
Remember to install reputable antivirus software, utilize firewall protection, enable 2FA, and regularly back up your data. By taking these steps, you can create a robust defense against malware and enjoy a safer digital experience.
FAQ
How Can Malicious Code Cause Damage?
Malicious code can cause damage by exploiting vulnerabilities in your system. It can steal sensitive information, corrupt or delete files, disrupt system functionality, install additional malware, or grant unauthorized access to cyber criminals.
What Can Malicious Adware Do?
Malicious adware can display unwanted and intrusive advertisements, redirect your web browser to malicious websites, track your online activities without consent, slow down your computer’s performance, and even collect personal information for targeted advertising or other malicious purposes.
How to Get Rid of a Virus?
A: If your computer has virus , follow these steps:
- Run a reputable antivirus or anti-malware scan to detect and remove the virus.
- Update your antivirus software to ensure it has the latest virus definitions.
- Quarantine or delete any infected files identified by the antivirus software.
- Restart your computer to ensure the virus is fully removed.
- Regularly update your operating system and software to patch security vulnerabilities and prevent future infections.
- Practice safe browsing habits, avoid downloading files from untrusted sources, and be cautious of email attachments or suspicious links.