With IT asset management software (ITAM), businesses should be confident in the knowledge that every asset is properly used, and in doing so, they’ll lock down the security and provide staff and customers alike with peace of mind.
And yet, research from Ivanti found that 43% of IT professionals are still tracking their IT assets in spreadsheets. It’s projected that by 2025, 45% of company data won’t be protected, despite requiring strong security. By letting this go on, businesses risk having their most vital data compromised.
In 2022, in order to safeguard their network and maintain security, IT teams need more than just spreadsheets to manage their IT assets. Let’s explore what IT asset management is and why it is just so crucial for hardware and software security.
What is IT asset management?
IBM defines IT asset management as the “end-to-end tracking and management of IT assets to ensure that every asset is properly used, maintained, upgraded, and disposed of at the end of its lifecycle.”
In short, making sure that valuable items, tangible and intangible, in your organization are tracked and being used. For avoidance of doubt, the three primary types of IT asset management are:
Hardware IT asset management
It goes without saying that physical hardware plays a role in an organization’s IT ecosystem. When we think of IT, this is probably where our minds go first and foremost. These assets include PCs, printers, copiers, laptops, mobile devices, servers, and any other hardware that is used for data management purposes within the company.
Hardware inventory management is important to prevent unnecessary complications with managing the devices in your network — especially if you have a lot. For the most part, mainframe modernization means that hardware IT asset management now means Universal Endpoint Management (UEM).
UEM tools can manage multiple employees and multiple machines from one central portal, making life much easier for IT managers. An intuitive dashboard can provide a wealth of info we need at a glance and in real time. For example, IT managers can get eyes on what devices are in the network, filter based on platform, activity or enrollment status, and take actions on them either individually or in bulk.
Admins can be notified about changes in device, meaning any potential problems can be caught before they become catastrophic. This might be when the device moves out of a compliant location, goes offline, or is running low on battery.
Digital asset management
In the constantly evolving landscape of cloud computing, digital asset management (DAM) plays a pivotal role, running parallel to the growth and diversification witnessed in SaaS, IaaS, and PaaS. As businesses increasingly store and manage a vast array of digital content such as images, videos, and documents in the cloud, DAM becomes crucial. It offers a centralized, cloud-based solution for organizing, accessing, and securing these digital assets. This alignment with cloud asset management strategies ensures streamlined workflows, enhanced security, and efficient resource utilization, making DAM an indispensable component of modern cloud infrastructure.
Software IT asset management
This is the most complex process of inventory management, as it involves compliance requirements, licensing, shadow IT, and IoT. We’re not just talking about downloading a Microsoft Teams app and being done with it. Software assets must be continuously monitored, reviewed, and updated to meet demands and a changing market.
Just as with hardware, UEM’s offer a database in which approved apps can be added or removed. Info about the apps — publisher, license type, category, price, version, status —- are then easily recorded within the same UEM used for physical assets. The whole lifecycle of onboarding, configuring, deploying, monitoring, and retiring can be managed from one place.
Admins can also control precisely which apps can and can’t be in the network (that’s a BIG no to Facebook on a work phone connected to the network).
Cloud asset management
Modern businesses aren’t limited to brick, mortar, and some installed apps. The cloud computing market is projected to be worth $947.3 billion by 2026, as more and more organizations move aspects of their business to the cloud. New Netsuite alternatives and competitors are appearing every day, and it’s not surprising as cloud software gains new momentum.
IT asset management is also used to track both cost and usage for cloud resources including software as a service (SaaS), infrastructure as a service (IaaS) and platform as a service (PaaS).
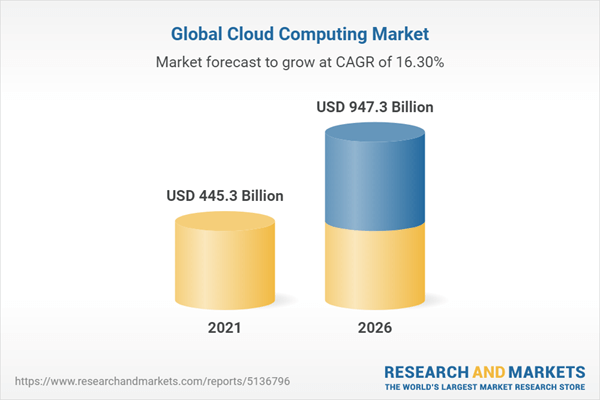
Image sourced from researchandmarkets.com
The most common, software as a service management, monitors the onboarding, licensing, and renewal of software that a company uses. Infrastructure as a service is less widely used, but is a model in which resources are hosted in a cloud environment instead of a data center. The final, platform as a service, provides a development and deployment platform in the cloud, which allows for the roll out of cloud-based apps.
Why is hardware and software security important?
Security. Secure. Safe. We’ve heard them mentioned that often they’ve almost become buzzwords.
But, the global web of interconnectivity is growing daily. More devices are joining the network. Electronic data interchange is on the up, allowing for more storage, faster connections and better communication.
It’s also adding risk. Cybersecurity Ventures predicts that global data will reach 200 zettabytes by the year 2025. At the same time, the firm projects a hefty $10.5 trillion in money lost to cybercrime annually by the same year. Security. Not a buzzword, but a requirement for businesses to protect both their bottom line and their customers.
In years gone by, IT departments could easily control their assets and remain secure. For the most part, IT departments, hardware, software, and employees were in the same building. Now, asset management extends far beyond the desk computer that’s issued on the first day.
Teams are now distributed: gone are the days when the back office helped with marketing campaigns. Modern workplaces require IT teams to adapt their asset management process to maintain security and best enable the business to grow in the new landscape.
How does IT asset management improve hardware and software security?
There is an abundance of documented process improvement methodology out there for IT asset management. Regardless of your approach, nail down your IT asset management, and you’ll almost certainly improve your hardware and software security.
This is because IT asset management:
Provides a single source of truth
There is no denying it: IT asset management creates a one-stop-show and a single source of truth. Without a defined process in place, assets will be tracked, but in a number of different places by many different people.
Efficient asset data management automation offers its consolidation, providing systems that do the work without the need for endlessly tracking down artifacts, monitoring usage, and interpreting dependencies.
It takes an average of 287 days to identify and contain a data breach.
Best chance to catch it earlier? Have everyone singing from the same song sheet.
By having everyone using the same procedure to manage different assets you’ll be better placed to pick up on any anomalies, troubleshoot, and track down the source of any breaches. This is especially important as 91% of businesses experienced a phishing attack in 2021.
Enables IT managers to adapt at scale
There has been a rapid technological transformation over the last few years, and it’s showing little signs of slowing now. Organizations with more than 60% of employees working remotely had a significantly higher average data breach cost than those without remote workers. But flexible working is here to stay, so IT managers need to be able to mitigate these risks.
IT asset management makes this possible. Not easy, but possible. When organizations did not adapt their IT to cope with the rise in remote working, the average cost of a breach was $5.02 million, as compared to the global overall average of $4.24 million.
As so many more assets are now being used outside of the office environment, asset management is essential to know which assets are being used, where they are being used, and if they’re being used correctly and securely.
Reduces risk and improves compliance
IT software providers have specific requirements for using their products, and companies that fail to follow those requirements could have to pay an arm and a leg in compliance penalties.
There really is no excuse, and costs for non-compliance with software licensing rules can be incredibly high.
By keeping on top of your IT asset management you can easily identify if you’re in compliance with all licensing requirements and make sure those licenses are not expired. You can also ensure that all software is updated when necessary which could help keep your data secure.
Supports IT teams to optimize product lifespans
IT assets have a limited lifespan. To maximize their value, organizations need to optimize the methods of managing them. The image below shows a traditional look at lifecycle management, provided by the National Institute of Standards and Technology (NIST). The asset lifecycle involves a continuous loop of monitoring, and without knowing when to maintain, modify and dispose, the life cycle comes to a halt.

Image sourced from csrc.nist.gov
Effective asset lifecycle management supports processes like change, incident, and problem management. With the right information available, teams can move more quickly and better predict impacts before they happen.
IT asset management is crucial for hardware and software security
Ultimately, IT asset management helps you keep your business secure. While businesses have optimized their methods of inventory control, many are falling short when managing their IT assets.
In order to safeguard your network and maintain security, you need a robust IT asset management strategy in place.



